Investigators started by Googling “fentanyl for sale” and then emailing sellers from six different websites as they...
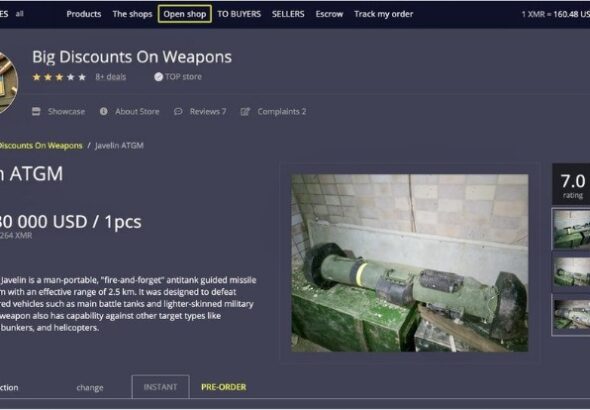
The analysis of Telegram’s black market showed that drugs are one of many illicit products traded on...
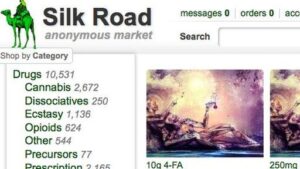
Since the dark web is a hidden and uncontrolled part of the web, there is a high...
But now consumers are in charge it will never be the same again. Dark net markets make...
In its liquid form, IMF can be found in nasal sprays, eye drops, and dropped onto paper...
A little more than half of the listings are for substances that are illicit, unregulated or diverted...
For maximum anonymity, you should tumble the digital coins you purchase. The operation implies using a service...
And cryptocurrencies add another layer of protection for those seeking to duck police suspicion. The country was...
David Khalaf is a writing, communications, and marketing professional with specialties in media, investigations, content strategy, and...
“I only talk about my mushroom thing in person or through Signal,” said the shroom dealer outside...