Therefore, if you do decide to explore it, exercise extreme caution. No one is hiding here—they’re just guaranteeing that people in censored countries can read the news without being flagged. There are often copious amounts of how-to articles, software exploits, and hacked credentials for sale. Not every visitor is a criminal, but this is where most cybercrimes begin. No user names are tied to actual identities, and no moderation like one may find on Reddit. Users leverage these platforms to organize protests, whistleblow, share survival guides, or share files P2P.

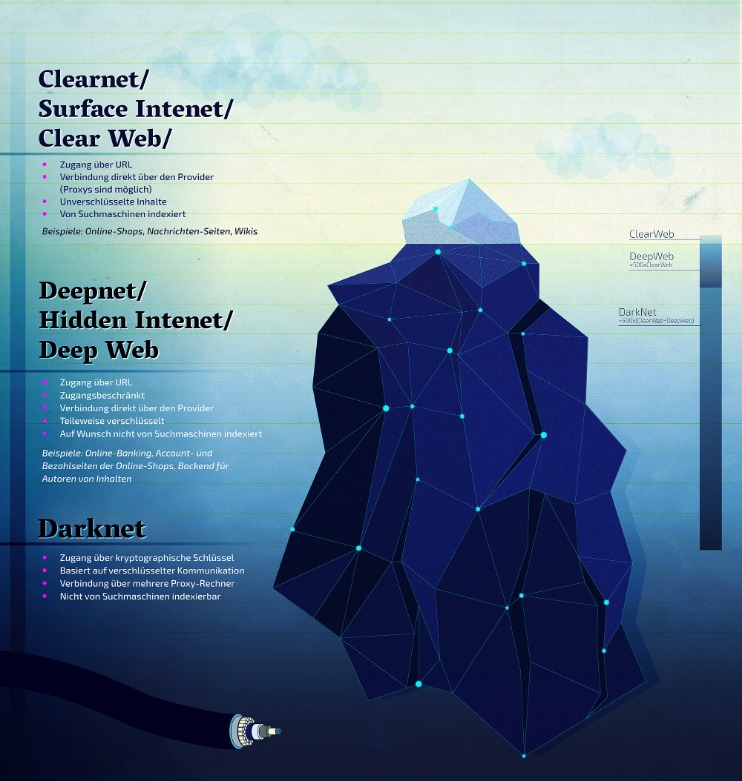
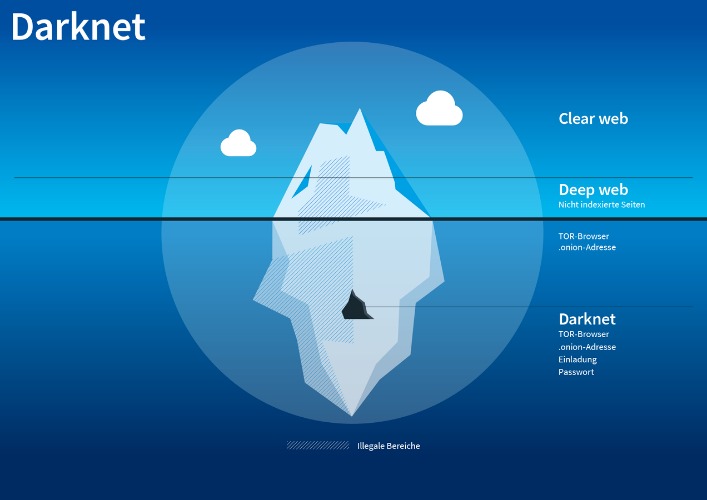
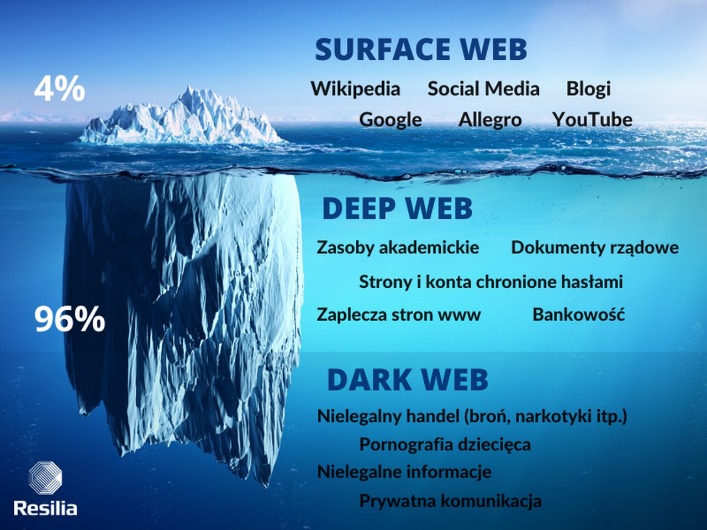
The deep web is made up of content that search engines such as Google do not index. Such data includes medical records, financial information, research papers, private forums and networks, and other content. Learn how darknet markets function and the challenges they present to cybersecurity, shedding light on the hidden side of the internet.
Never Use Your Credit And Debit Card For Purchases
It’s been a constant back-and-forth between cybercriminals and law enforcement, with each new site trying to be smarter and more secure than the last. Today’s cybercriminals spread their activities across multiple platforms, making them harder to track and shut down. In the first arc of the anime series Lupin the 3rd Part V, Lupin III steals digital currency from the “Marco Polo” darknet market. Then, you can set up 2FA (two-factor authentication) for that extra touch of security in case someone somehow figures out your password. If you ever have to connect to public Wi-Fi, make sure to use a VPN to keep your browsing safe and private. According to a recent trend, the dark marketplaces faced a decline in revenue.
- Additionally, Tor exit nodes are often blocked by websites that don’t trust them, and Tor over VPN can’t do anything about that, either.
- As I’ve mentioned, the dark web isn’t just a place of eternal torment, teeming with drug dealers, human traffickers, and a hitman.
- It’s known for its strong security features (like a trusted escrow system, PGP two-factor authentication) and anonymity.
- Abacus Market is one of the newer darknet marketplaces that quickly filled the gap left by AlphaBay’s takedown.
- The best way to protect yourself from the dangers of darknet markets is to simply avoid them altogether.
- You can choose to monitor just your Google Account email address or add other information to your monitoring profile.
Types Of Dark Web Sites (and What Really Goes On There)
Ultimately, this disruption to accessibility is not a unique event. In fact, it is routine for individuals participating in these dark web communities, par for the course of engaging in the markets. But those of us who have studied this space for years weren’t surprised.
Also, previously, the Tor browser was vulnerable to JavaScript attacks as it provided hackers a pathway to track your activities by using the session details. Therefore, for security reasons, disable JavaScript on the Tor browser and enjoy an anonymous browsing experience on the dark net. In 2013, the FBI shut down the Silk Road, but it was later relaunched in 2014 with the new name of Silk Road 2.0, but the German authorities shut it down in the same year. Other than the Silk Road 2.0, similar marketplaces also emerged, but they all went down sooner or later.
However, when it comes to darknet markets, the story is very different. Dark web marketplaces are mostly hubs for illicit goods and activities, posing serious risks to users and the wider community. Abacus Market is one of the newer darknet marketplaces that quickly filled the gap left by AlphaBay’s takedown. It hosts over 40,000 listings and offers everything from illicit goods and substances to hacking tools. With an estimated market value of around $15 million, it has grown into a massive hub for cybercriminal activity.
Tor2door Market

And while the dark web isn’t synonymous with illicit activities, it’s undeniably the breeding ground for the internet’s black markets, hacker forums, malware vendors, and other illegal activity. Therefore, you must know how to access dark web marketplaces safely (covered later in this article). Despite Telegram’s anonymity, the dark web is still a hot spot for illegal trading of malware, illicit goods, and stolen data (such as stolen credit card information).
The Role Of Forest VPN
However, the trend is clear—illicit actors are expanding their strategies, forcing enforcement agencies to evolve their tracking methods to keep pace with increasingly sophisticated laundering techniques. There are a few reasons why the dark web isn’t stopped or shut down. First, it’s difficult to track and monitor activity on the dark web since much of it is encrypted. Journalists and whistleblowers, including Edward Snowden himself, often use the dark web and Tor to exchange sensitive information. For instance, the Ashley Madison data dump was posted to a site only accessible to Tor users.
Dark Web Marketplace Links
Its interface makes it easy to identify clone websites and ensures that users always use the authentic site. It’s a user-only marketplace, meaning you need to register to enter. During our tests for the research, we were able to register with a bogus email and a random username. All that one can expect from a deep web marketplace when it comes to anonymity and security. Since the dark web can be accessed through the Tor browser, use a VPN with the Tor browser to ensure increased protection.
The content of all these pages is stored on Google’s servers, but it’s mostly outdated, old content; smartphone app content; journals; court records; private social media profiles, and much more. Ethically, they must minimize harm, responsibly handle any stolen or sensitive data (often notifying victims or law enforcement), avoid entrapment, and maintain research integrity. Discover how to explore darknet market links safely while ensuring your privacy and security. BidenCash and other exit-scam markets such as Torzon and Kingdom Market collapsed between 2022 and 2024. They used “free data dumps” and emotional marketing to build trust before vanishing—an enduring lesson in the risks of social engineering. BriansClub remains a long-standing credit card data shop since at least 2014.
Exploring The Use Cases Of Darknets & Dark Markets
However, your online activity is encrypted and hidden from view thanks to Tor’s onion routing. This means your ISP can’t see that you’re accessing the dark web (or indeed, the specific sites you’re accessing). Unlike Tor, however, it cannot be used to access the public internet.
What Is Kubernetes And Containers? Why Is So Popular?
Many experts advise against using third-party mobile browsers that utilize the Tor Network. The dark web, or dark net, is a small part of the deep web that is kept hidden on purpose. Websites and data on the dark web do typically require a special tool to access. In repressive regimes, darknets play a vital role in enabling free speech and access to uncensored information. Tools like Tor are used to bypass government-imposed firewalls and surveillance, ensuring open communication. The significance here is the preservation of civil liberties and the right to information.
- These sites often look basic or outdated, and their URLs are lengthy strings of random letters and numbers.
- The dark web is a subset of the deep web that is intentionally hidden, requiring a specific browser—Tor—to access, as explained below.
- Despite multiple takedown efforts by law enforcement and security researchers, Brian’s Club has resurfaced repeatedly and continues to add new stolen credit card data.
- The research used appropriate sources of data and effective practices to analyze the data to secure its validity and reliability.
- You can now safely browse dark web websites and hidden wikis, but if you plan to do anything more than that, you’ll need to take several precautions.
- This study was conducted using Central Michigan University’s policies and procedures.
Financial Institutions
The dark web allows people to access and share all sorts of illegal and explicit material without judgment or censorship. The Tor network was created by the US military in the 1990s for anonymous communication between spies over the internet. That effort was never fully realized, but the US military published the code under a free license in 2004. Researchers from the Electronic Frontier Foundation and other groups continued its development and launched the Tor project in 2006 as a tool for journalists, activists, and whistleblowers.
Do I Need A VPN To Use The Dark Web?
The marketplace requires merchants to pay fees to sell their products, helping ensure a certain level of quality control. Here’s a look at the top 10 dark web markets currently dominating this underground space. If the VPN connection fails, the automatic kill switch will kick in, temporarily breaking your traffic. ExpressVPN is an excellent choice for Tor and accessing the Dark Web.



