While the deep web usually requires just a username and password to be accessed (think of your email inbox), the dark web cannot be reached without the right software or hardware. Kurt Baker is the senior director of product marketing for Falcon Intelligence at CrowdStrike. He has over 25 years of experience in senior leadership positions, specializing in emerging software companies.
- The deep web is part of your everyday web and thus has to comply with all sorts of security standards and be hosted by companies that have at least some interest in maintaining their users’ privacy.
- This makes it hard to use the Tor browser for surface web activities that require fast speeds (such as streaming, gaming, torrenting, making private calls, etc.).
- Just as you need the right tools to access the dark web, you also need the right protections to be able to stay safe on it.
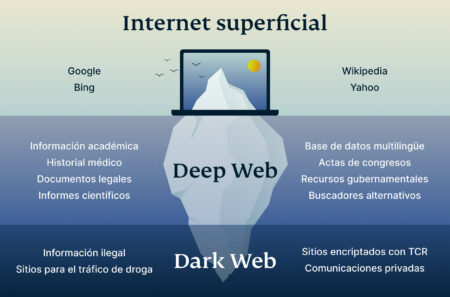
- Many mistakenly believe the Deep Web and Dark Web are synonymous but they are distinctly different.
- Even if these resources are indexed by the search engines, one must possess credentials to be able to access the pages or sites that are guarded through authentication.
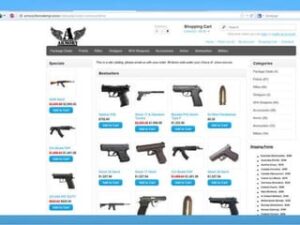
Some examples of legal uses include secure communication for people living in oppressive regimes, communicating with journalists privately, and conducting sensitive discussions on private forums. Think password-protected websites, subscription services, banking portals, and even the private contents of your email inbox. The Dark Web is a small part of the Deep Web, accessible only through specialized tools like Tor (The Onion Router). Unlike the Deep Web, it is designed to offer anonymity and is often linked with unregulated online activities, although it also supports legitimate uses. On the other hand, the dark web welcomes more distinct groups of users, like criminals, whistleblowers, or political dissidents, who leverage off the anonymity the dark web provides. With that said, any regular internet user can visit the dark web, which is not illegal to use.
Web Hosting Company Increases Security Team Bandwidth With Up To 80% Decrease In Threat Research Times
Major differences between the two include accessibility, purpose, security level, content type, user intent, and possible legal implications. Through Tor, users can access a number of dark web websites, including mirrored versions of surface web sites such as Facebook and The New York Times. For those who really want to explore the dark web, several pages called the Hidden Wiki serve as a directory of links to other .onion sites.
There is no way to measure the exact terabyte amount, as much of this data hides behind secure servers. Countries differ in how aggressively they monitor Dark Web activity. In some authoritarian states, accessing Tor nodes can flag you for surveillance. Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing. Moreover, the anonymity that protects users can also be a double-edged sword.

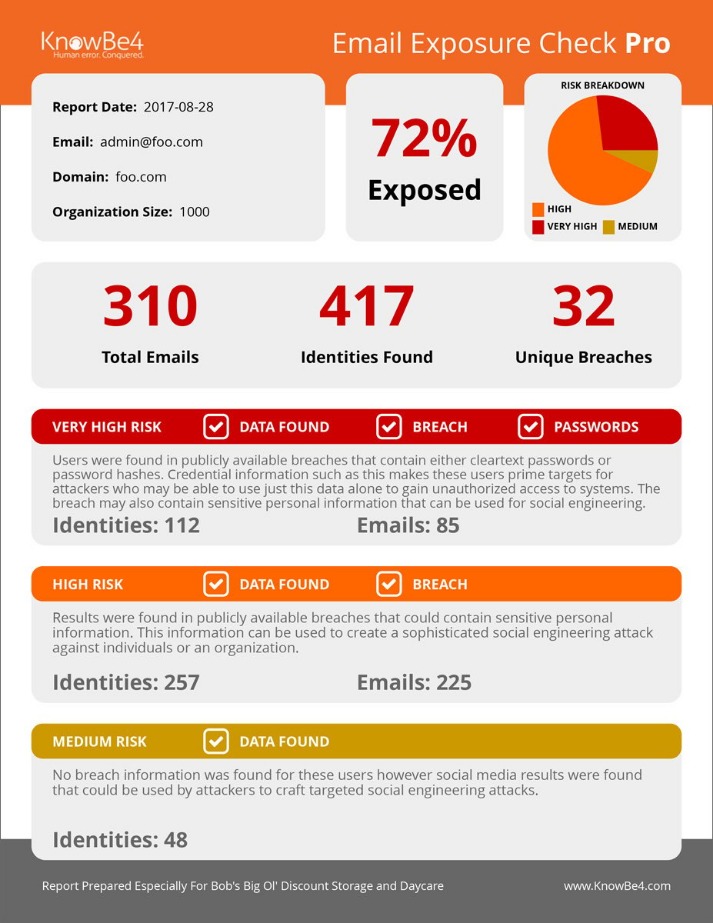
Strong Authentication And Password Management
Dive into the intriguing world of the Deep Web and Dark Web to understand their differences, purposes, and potential risks. Whether you’re curious about the hidden layers of the web or seeking clarity on popular myths, this guide will demystify the unseen side of the internet. Many of the email addresses and identities of your organization are exposed on the internet and easy to find for cybercriminals. With that email attack surface, they can launch social engineering, spear phishing and ransomware attacks on your organization. KnowBe4’s Email Exposure Check Pro (EEC) identifies the at-risk users in your organization by crawling business social media information and now thousands of breach databases. You need special software to access the Dark Web because a lot of it is encrypted, and most of the dark web pages are hosted anonymously.
Deep Web Vs Surface Web: What’s The Difference?
It prevents other people from accessing your Internet connection and also prevents websites from knowing about your physical location. Security teams often focus on dark web monitoring while overlooking equally critical deep web sources like GitHub or Telegram. However, threats can often originate in the deep web before escalating to the dark web.
What Is The Dark Web And How Do You Access It?
Therefore, those who want to express themselves freely without fear of reprisal from government bureaucrats must remain hidden. As a result, dark web enthusiasts will likely create more sophisticated techniques to prevent detection. This may be accomplished by password-protecting sites that are only accessible to those who pay and restricting access to specific IP addresses. H25.io is a premium directory in the Tor network, offering access to a diverse and meticulously curated list of onion sites. Our mission is to simplify navigation in the complex and evolving world of the darknet.
Now, Let’s Understand The Difference Between The Deep Web And Dark Web
The Surface Web refers to the portion of the internet that is easily accessible through traditional web browsers. This part of the web is indexed and easily searchable by popular search engines like Google, Bing, and Yahoo. Phishing attacks are prevalent, where users are tricked into revealing personal information or login credentials.
Falling for these scams can result in financial loss, identity theft, and even physical harm. Engaging with fake hitman services may expose individuals to dangerous criminals, while falling for phishing scams can lead to identity theft and financial ruin. Sooner or later, some of your data will spill over to collections available for sale on the dark web. What you can do to protect yourself is to make sure that data is not accurate anymore, not detailed enough to cause harm, and that you have multi-factor authentication enabled everywhere you can use it. Having reliable anti-malware protection active is also very important. Returning to cybersecurity issues, I need to stress that the dark web is a dangerous place, especially if you’re a non-technical person just looking to satisfy a curiosity.
Exploring the dark web can expose users to the risk of identity theft, financial fraud, and privacy breaches. Hackers and criminals often lurk on the dark web, targeting unsuspecting visitors with malware and scams. As such, it is essential to assess the potential risks before delving into the dark web to ensure adequate cybersecurity measures are in place. The risks of accessing the Dark Web include exposure to illegal content, potential scams, malware, and legal repercussions if one inadvertently engages in illicit activities. It includes legitimate resources such as academic databases and private networks, as long as users respect privacy laws and do not engage in unauthorized activities. The dark web is a part of the internet that provides anonymous and secure communication channels that can only be accessed with a special browser called Tor.
Google Removes Malicious Android Apps With 19 Million Downloads
To access the dark web anonymously, use a secure VPN service along with the Tor browser, as Tor networks are prone to ISP blocking. If you live in a country where Tor is banned, unblock Tor through mirror sites. Phishing sites or malware can be used to gain access to your login credentials potentially leading to data theft or account takeover.
It has its own deep web, as dark web websites come with user accounts and other private areas. The dark web is a smaller, intentionally hidden part of the internet that requires special software (like the Tor browser or I2P) to access. It is designed to provide anonymity to both users and site operators.
RESOURCES

I won’t elaborate on the specifics of social science currents and ideological sides here since it’s not the time and place. But you can read more about it, if you want, in this well put Vox editorial. Well, the funny fact about this is that the so-called intellectual dark web doesn’t have anything in common with cybersecurity issues or non-indexed pages. This is allegedly a layer of internet even deeper than the dark web, the well-known hub for criminal activity. Rumors say that this shadow web is a place where even darker, more serious criminal activity takes place.
Best Practices For Browsing The Deep And Dark Web Safely
Choosing the right Cyber Threat Intelligence platform can be the best weapon to win the war and protect your organization and customer data. Deploying a CTI solution will allow you to monitor and gather data on what’s happening on the Deep and Dark Web get alerts on activity specific to your organization. Fraudsters who have hacked into systems and stolen data oftentimes turn to the Dark Web to sell what they’ve gathered.