For the record, there are more scam sites for every genuine one, and it’s good to have a discussion forum about this. OnionShare is one of the best tools for that purpose, whether on the surface or deep web. The service remains free to use, and the secure design prevents access to third parties, eavesdroppers, and other malicious agents. To contribute a tip, join the community, which can be done anonymously through an approved onion link.
Using Onion Over VPN — All You Need To Know
In exploring the top 10 dark-web marketplaces in 2025, we’ve examined their core operations, diverse use-cases, inherent risks, and evolving trends. Cryptocurrencies, while offering enhanced privacy, also present significant risks. Users face vulnerabilities like market volatility, scams involving fake escrow services, compromised wallets, or theft through phishing schemes targeting crypto transactions. Furthermore, inexperienced users unfamiliar with secure cryptocurrency practices are particularly susceptible to these threats, risking the loss of their entire funds.
Market Value And Popularity

The site also uses strong encryption to protect against cyberattackers, such as anti-DDoS protection. It doesn’t use JavaScript, which goes a long way toward keeping you anonymous. Unlike other search engines, it does not collect or share web activities and personal data of users.
Keep Your Identity Hidden
OnionLinks is a curated dark web directory updated frequently with working .onion URLs. It categorizes links by function — markets, forums, search engines, privacy tools — and also includes uptime indicators. What sets it apart is its clean design and regular link testing, which reduces the chance of landing on broken or harmful pages. It’s a go-to for users who want structure and security in their dark web exploration.
Detailed Overview Of Each Search Engine
The site’s unique—loads fast, looks sharp, and vendors get treated right, keeping turnover low. I’ve used it; shipping’s discreet—plain packages or DeadDrops—and uptime’s been flawless, rivaling Abacus. It’s not as community-driven as Bohemia, but the polish makes up for it—feels like a pro operation, not a fly-by-night deal.
How To Avoid Phishing Scams And Malware Threats
NoScript and HTTPS Everywhere extensions provide additional protection against malicious scripts and unsecured connections. TorLinks maintains one of the most reliable directories of verified .onion sites. Its strength lies in regular updates and community-driven verification of links. I especially like how TorLinks categorizes links based on their type, letting you easily find what you need. Freshtools is a unique marketplace in that it does not only provide the stolen data, but it allows criminals to purchase MaaS which can cause further damage to the victims. It is one of the most active and up to date markets and always provides new and updated malware and data.

Essential Security Measures
- Buyers can enable two-factor authentication, and transactions are protected by escrow, including multisignature escrow for added safety.
- But before we start, install Norton VPN to help protect your digital identity and stay safer online.
- Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity.
- The dark web is a mysterious place that can only be accessed with specific tools and services.
Therefore, you will always find updated search results while using this service. To send a message or image via ZeroBin, you just need to copy the desired content and paste it into ZeroBin’s editor. The editor will then create a link for you to forward to the sender. For those needing an additional layer of security, you can set it to disappear right after viewing.
In 2021, they showed how tax rates benefit the rich, and they relied on stolen or leaked IRS documents to do so. In addition to the surface web, ProPublica also hosts their site on the dark web, because they want to make sure that everyone can access their reporting. A robust antivirus can help block malware and other online threats, even on the dark web. They use pseudonymous wallets, privacy coins (like Monero), mixers, chain-hopping, and non-KYC platforms to obscure transaction trails. Cybersecurity experts should pay close attention to these trends, as they often indicate emerging threats and profit-generating tactics among the cybercriminal forums. One of the most common is the exit scam, where a marketplace suddenly disappears and takes everyone’s money with it.
But if you are thinking you can find links to the deepest part of the dark web using this site, it’s not that simple. However, there’s no guarantee that all the links on this site are working. Some may lead to malicious sites, downloading malware on your device. The Tor browser is the most preferred browser for surfing the dark web because it creates encrypted pathways for user traffic, ensuring all the activities are anonymous. The dark web is not easily accessible, especially with browsers like Chrome or Safari, as it requires specialized protocols like Tor’s onion routing.
This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacySavvy.com page. X Funds derived from non-crypto native crime, except for cases brought to our attention by customers. Because these transactions are impossible to identify as illicit without more information. This article delves into the current state of darkweb markets, backed by statistics, comparisons, and predictions for the years 2024 and 2025. Breaking Bad Forum is a community of the best chemists from all over the darknet. On the forum, you can buy and sell reagents, drugs, and study guides on synthesis, and get advice from expert chemists…

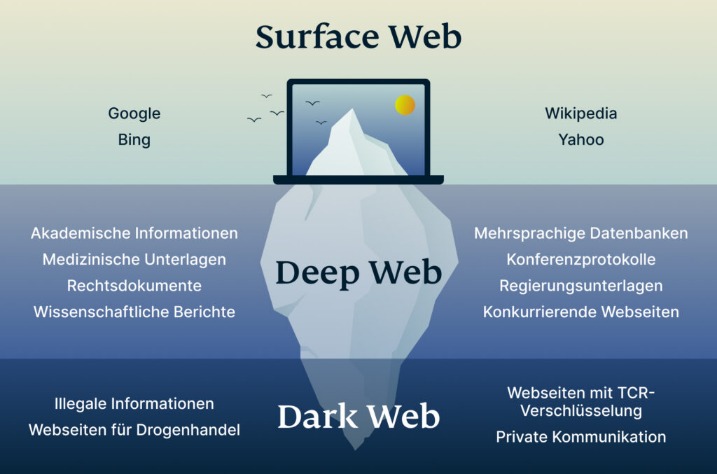
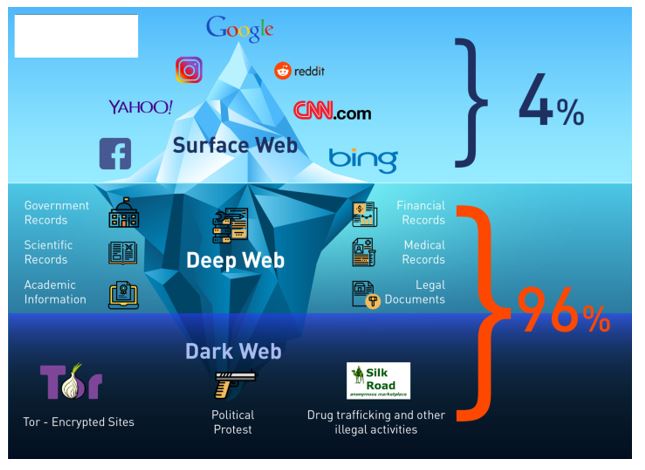
But if you use antivirus software, avoid clicking shady links, and stick to known sites you should be okay. It’s also a good idea to set up a VPN for an extra layer of protection. You can access onion sites only through the Tor browser or special network configurations. On the Tor network, the onion domain name reflects the fact that, like the layers of an onion, the Tor browser consists of layers of protection. Tor encrypts traffic, masks your IP address, blocks trackers and browser fingerprinting, and doesn’t store a record of your activity. In the image above, (a) is the surface web, which includes publicly visible websites like blogs, shopping sites, and news sites.
Simply put, accessing and browsing the dark web is perfectly legal. For example, it maintains your privacy and enables you to access untraceable content and services. Just like Google, the dark web has some search engines present on it.
If you spend most of your time online (who doesn’t, really?), you might have come across the term dark web before. The mystery surrounding it creates a lot of curiosity among people and the chances are that you’re one of them as well. Smart people never get caught since they know how to anonymize themselves, but the new user faces difficulty. So you have to use the dark web with whatever security precautions you can manage. Just don’t be stupid and ruin your lovely life by doing foolish things.
🛑 Other Dark Web Vendors (For Awareness Only)
It assigns a task to the client instead of the server, eliminating server-related vulnerability. Wasabi is one of the most popular cryptocurrency wallets on the dark web. It allows you to search for images, maps, files, videos, social media posts, and more. It aims to advance research on terminal illnesses like cancer with access to unbiased scientific publications.
Darknet markets trace their origins to the early 2000s, with the advent of Tor in 2002 by the U.S. Not all onion sites are dangerous, but many host illegal, harmful, or deceptive content. Stick to trusted sources and use caution when navigating the dark web. Unfortunately, many dark web websites are devoted to the illegal trade of leaked personal information.