The dark web contains numerous security risks, from malware to scams and illegal content. Thankfully, there are...
wpadmin
Users leverage these platforms to organize protests, whistleblow, share survival guides, or share files P2P. The good...
The Kilos search engine is primarily used to find and access dark web markets where illicit drug...
Its categorized structure saves time compared to random searches, but the outdated links and scam risks keep...
Note that we determined if 2 listings are identical by matching the same elements (ie, listing’s title...
Individuals who seek CSAM on Tor search engines answered our survey that aims at developing a self-help...
The goal of buying stolen credentials is frequently to open lines of credit in someone else’s name....
These platforms leverage advanced encryption technologies, decentralized systems, and user-friendly interfaces to ensure seamless transactions. The integration...
Finally, in the model refining stage, the model is trained for other 2 iterations using the same...
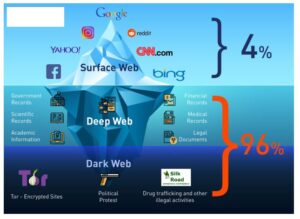
Short for “The Onion Router,” Tor uses the decentralized onion routing network to allow users to browse...