It’s a wake-up call for all of us to be more vigilant about our online security. It’s a marketplace where sellers offer a range of Credit Card Dumps for sale, often including details like the card’s balance and country of origin. This password unlocked the credit histories and personal information of many Sears customers, which were subsequently used to obtain their credit card numbers. This type of card has been around for decades, with the first credit cards emerging in the 1950s.
What Stolen Cards Are Used For
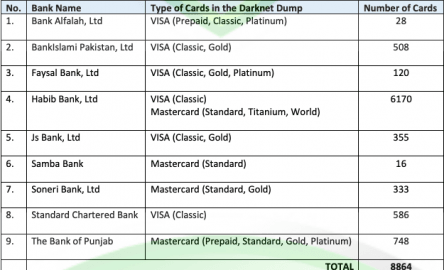
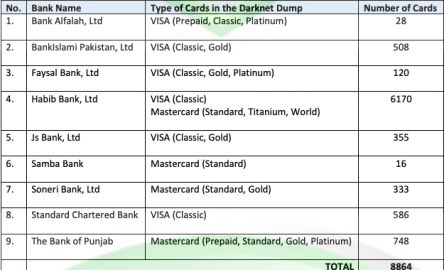
The cybersecurity community is on high alert as B1ack’s Stash, a known marketplace on the dark web, has announced a massive leak of 4 million stolen credit card details. A Credit Card Dump typically refers to stolen credit card information that has been copied electronically, often through hacking or skimming devices. Fraudsters use this data to create counterfeit credit cards or make unauthorized online purchases. B1ack’s Stash, on the other hand, emerged in 2024 and quickly gained attention by releasing millions of stolen credit card details for free—a tactic often used to attract cybercriminals.
Working with Changelly is a pleasure, thanks to their professional and courteous approach. Use this guide to learn how to easily automate supply chain risk reports with Chat GPT and news data. These details are needed for physical use such as withdrawing money from ATMs.
STYX Market
The Australian Federal Police is also running two inquiries into who obtained and attempted to sell the data and protections for more than 10,000 customers whose records were posted online. Several investigations have been launched into the massive data breach, which compromised the personal details of millions of Australians. The key is catching this activity before large volumes of card data make it to market. Some threat actors even run automated validation services that check card numbers before the sale, guaranteeing their buyers a certain percentage of “live” cards. I can’t say for certain, but I’ve always seen carding as a more ‘hardcore’ form of cyber crime—at least from a criminal’s perspective. Compared to harvesting phone numbers or email addresses, carding demands more risk, and potentially, more reward.
Individuals:
Criminals obtain this data through various methods, such as skimming or hacking into payment systems. Once obtained, the stolen credit card data is resold to other individuals or criminal organizations on the dark web. When credit card data is dumped, it often ends up on the dark web, where it’s bought and sold by criminals. The information can be used in multiple ways, such as making unauthorized purchases or even creating counterfeit cards for further criminal activities. Moreover, cybercriminals may combine stolen credit card numbers with other sensitive data, like Social Security numbers or addresses, to commit more sophisticated types of identity theft. These examples illustrate not only the scale and impact of credit card dumps but also the need for companies and consumers to remain vigilant against cybercrime.
- Credit card fraud on the dark web operates quite differently from what many people imagine.
- Established in 2019, Russian Market is a well-known and highly regarded data store on the dark web, specializing in the sale of PII and various forms of stolen data.
- There is some uncertainty about how many of the cards are actually still active and available for cybercriminals to use.
- Physical cards, on the other hand, are cloned from stolen online details and can be used to withdraw cash from ATMs.
- Hijacking a PayPal account requires a different approach than stealing a credit card number.
With just a few taps, people can see exactly where their money goes and catch problems early. Some of the carding activity has continued to expand beyond the dark web. All websites hosting pornography will have to check the age of their users from Friday. This new trend for marketplaces winding down in an orderly fashion is known as “sunsetting” or “voluntary retirement”.
Student Loan Breach Exposes 25M Records
Much like the situation after Silk Road was taken down, out of the ashes of Joker’s Stash, we have seen dozens of new carding data providers crop up, some specializing in particular regions or types of card data. Over the past decade, Joker’s Stash emerged as one of the most infamous dark web marketplaces, gaining notoriety for illicit transactions and offering a plethora of stolen financial data. The platform, distinguished by the sophistication of its administrators, left an indelible mark on the cybercrime landscape, and became the central marketplace for stolen card data, outclassing all competitors.
How Dumps Credit Cards Work
Some dark web marketplaces even host content that’s not just illegal but extremely harmful, so it’s really important to understand the risks before diving in. People generally think about a credit freeze as something to do if their information has been stolen, but Myroup says doing it before you have a problem can be a preventative measure. It’s a fairly simple process of reaching out to the major credit bureaus, and it won’t cost you any money or negatively impact your credit score. The downside is that if you decide to get a mortgage or a new credit card, you’ll have to unfreeze your credit before you can apply. A free Dark Web scanner like the one offered by Identity Guard can provide this information quickly and easily — but it won’t show you all of the information to which hackers have access.

Understanding Dark Web Websites For Credit Cards

If you notice anything suspicious, report it to the establishment and contact your bank. Established in 2022, WizardShop is one of the biggest data stores on the dark web, focusing mainly on carding and financial data. Russian Market has consistently remained one of the most popular and valuable data stores on the dark web. The platform’s activity has increased significantly over the past year, indicating its growing influence and market share in the underground economy.
How To Protect Yourself From Dark Web Dangers
Upgrading to a paid membership gives you access to our extensive collection of plug-and-play Templates designed to power your performance—as well as CFI’s full course catalog and accredited Certification Programs. This gives security teams time to adjust their defenses before new techniques become widespread. Another important aspect is understanding your exposure when third-party breaches occur. Monitoring these sites also helps track the effectiveness of security investments.
Card Data And Markets
If the company you’re buying from doesn’t have your sensitive card information, neither will hackers that hit that merchant with a data breach. But you can face criminal charges if you use the dark web to sell or purchase illegal firearms, drugs, pornography, stolen passwords, hacked credit card account numbers, or other items. Here’s a guide that will help you learn about the dark web, the sites that populate it, and how you can visit it safely using the added protection of a VPN and antivirus software.
How Many Cards Are Still Active?
The sooner you become aware of compromised information, such as stolen credit card numbers on dark web, the faster you can take steps to mitigate damage. Rapid response can prevent unauthorized transactions, minimize financial losses, and protect your customers’ trust in your business. The dark web market for stolen credit card information is a growing concern for consumers and businesses alike. Consumers are advised to protect themselves by monitoring their account statements regularly, using virtual credit cards, and practicing safe online shopping habits. Companies should invest in robust cybersecurity systems and quickly respond to any potential breaches to minimize the damage caused by data dumps. A credit card dump is a significant cybercrime in which an unauthorized digital copy of credit card information is stolen and sold on the black market.
Companies that suffer from data breaches caused by credit card dumps face various costs, including remediation expenses, notification fees, legal liabilities, and reputational damage. In some cases, these expenses can run into millions of dollars and may lead to significant losses in revenue or even bankruptcy. Cybercriminals will use this kind of rich data grab to target you with additional attacks. They use a term known as “Fullz” in underground online forums and dark web marketplaces, where cybercriminals buy and sell stolen personal information.