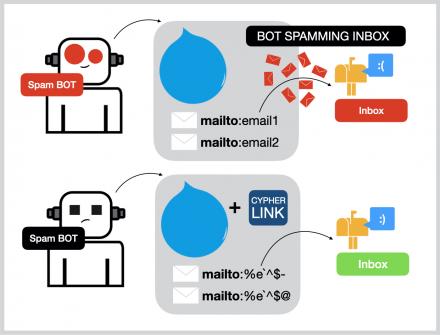
Cypher’s offerings are further enriched by unique custom hacking services, malware, and coveted data dumps, affirming its pioneering status in the darknet market space. Unlike other online file sharing tools that might expose your files to security vulnerabilities or data breaches, 0xCipherLink ensures end-to-end encryption. Your files are encrypted locally on your machine before being sent over the network, ensuring that only the intended recipient can decrypt and access them. It also works on all platforms, weather its an windows machine, linux, mac, or an android phone. MERGE can be used in conjunction with preceding MATCH and MERGE clauses to create a relationship between two bound nodes m and n, where m is returned by MATCH and n is created or matched by the earlier MERGE.
Conditional Expressions(CASE)
Grant SHOW PRIVILEGE privilege to list privileges to the specified role. Grant REMOVE PRIVILEGE privilege, allows the specified role to remove privileges for roles. Grant ALTER ALIAS privilege to alter aliases to the specified role. Deny SET PASSWORD privilege to alter a user password to the specified role. Grant ALTER USER privilege to alter users to the specified role. Grant SHOW ROLE privilege to list roles to the specified role.
Why Does The Analyzer/recognizer Not Detect My Cipher Method?
We’re not just a platform – we’re a community of passionate cypher url enthusiasts and cypher darknet market connoisseurs who are committed to pushing the boundaries of what’s possible. Through strategic partnerships, cutting-edge technology, and a deep understanding of customer needs, we’re laying the foundation for a new era of cypher website shopping. Imagine a world where discovery, personalization, and unparalleled convenience are the norm, and where your every cypher url and cypher darknet market desire is effortlessly fulfilled.

Grant SHOW TRANSACTION privilege to list transactions by the specified users on home database to the specified roles. Grant SHOW TRANSACTION privilege to list transactions on all users on all databases to the specified role. Deny CREATE NEW TYPE privilege to create new relationship types on all databases to the specified role. Set the default Cypher version for a remote database alias when creating it. List all database aliases in Neo4j DBMS and information about them, returns only the default outputs (name, composite, database, location, url, and user).
It has primenumber generation functions, a hash function, RSA keygenfunction and encryption-decryption functions for RSA. This secure communication platform is designed to handle the transmission of sensitive data with the utmost security. Using end-to-end encryption and rigorous data integrity checks, it ensures that your information is protected against any unauthorized access. Since 2020, 2easy has sold massive stealer logs with sensitive data like passwords, bank cards, and initial access credentials.
Names of returned columns can be aliased using the AS operator. Relationship pattern filtering on the ACTED_IN relationship type. Approach unexpected challenges in Cypher by staying updated on new techniques, practicing regularly on platforms like HackTheBox, and collaborating with the cybersecurity community for insights. Adapting a problem-solving mindset and continuous learning will help tackle any surprises that come your way. Embarking on Cypher, a medium-difficulty Linux machine on HackTheBox, offers a rich exploration into web application vulnerabilities, network service misconfigurations, and privilege escalation techniques. This comprehensive writeup delves into each step of the penetration testing process, expanding upon initial reconnaissance with detailed analysis and exploitation.
Write-Only Query Structure
Create a standard database named topology-example in a cluster environment, to use 1 primary server and 0 secondary servers. Create a point index with the name given by the parameter nameParam on relationships with the type STREET and property intersection.Point indexes only solve predicates involving POINT property values. Create a text index on relationships with type KNOWS and property city.Text indexes only solve predicates involving STRING property values. Create a range index with the name index_name on nodes with label Person and property name.
Functions
Microsoft Azure customers worldwide now gain access to Active Cypher Cloud Fortress to take advantage of the scalability, reliability. Provides an automated monitoring system for the transcation process. Cypherpunk Holdings, Inc. engages in the investment in technologies and crypto currencies with strong privacy.
- Grant SET USER STATUS privilege to alter user account status to the specified role.
- Grant TRANSACTION MANAGEMENT privilege to show and terminate transactions on all users, for all databases, to the specified role.
- Unlike other online file sharing tools that might expose your files to security vulnerabilities or data breaches, 0xCipherLink ensures end-to-end encryption.
- The USE clause determines which graph a query is executed against.
- Cypher ventures boldly into an array of product categories beyond the commonplace, spanning drugs, fraud, hacking, counterfeits, and defense/intelligence sectors, each thoroughly categorized.
Custom Code Creation
The user interface of Cypher market is arguably its least commendable aspect. Despite a recent overhaul, the interface has regrettably deteriorated rather than improved. The website is only functional on computers and other devices with large screens, and the interface lacks any responsive design elements.
- Our AR capabilities will revolutionize the way you shop, allowing you to see how items will look and fit in your environment, ultimately enhancing your overall cypher url experience.
- The duration.inMonths() function returns the DURATION value equal to the difference in whole months between the two given instants.
- Map projection with an all-map projection to project all key-value pairs from a MAP without explicitly listing them.
- The AI encryption detection program is based on a multilayer perceptron (MLP).
- Because a Person node with the name “Greta Gerwig” already exists, this query will only SET the dynamic labels added to the ON MATCH subclause.
- In contrast to conventional markets, Cypher does not operate an account wallet system and instead processes all payments on a per-order basis.
Some versions even include historical codes like the Pigpen cipher or Morse code. This translator is a lifesaver for creating authentic coded messages in my detective novels. I can quickly generate different types of ciphers that actually work, which adds an extra layer of realism to my stories. Produce complex encrypted messages using keyword-based polyalphabetic substitution for enhanced security.
1 Password Cracking Techniques
The date.transaction() function returns the current DATE instant using the transaction clock. The date.statement() function returns the current DATE instant using the statement clock. The date.realtime() function returns the current DATE instant using the realtime clock. The character_length() function returns the number of Unicode characters in a STRING.This function is an alias of the size() function. The char_length() function returns the number of Unicode characters in a STRING.This function is an alias of the size() function.
SHOW SETTINGS
It exclusively supports Bitcoin (BTC), Monero (XMR) for transactions, emphasizing the importance of privacy and security, and features a direct payment system for each purchase, catering to the needs of privacy-focused users. The translator supports multiple popular encoding methods including Caesar cipher, Vigenère cipher, and substitution ciphers. You can create custom letter-to-letter mappings, use numeric codes, or implement symbol substitutions. The tool also handles special characters and spaces, making it versatile for different coding needs.

Tools like Python scripts play a crucial role in solving Cypher challenges. The walkthrough for understanding how to identify vulnerabilities like command injection is key. This knowledge aids in decrypting encrypted data and unraveling hidden clues within the Cypher challenges.
Quantified relationship matching paths where a specified relationship occurs between 1 and 10 times. Create a relationship with the given relationship type and direction; bind a variable r to it. The UNION clause can be used within a CALL subquery to further process the combined results before a final output is returned.
If a relationship with that type is created without a when property, or if the property when is removed from an existing relationship with the type LIKED, the write operation will fail. Create a point index on nodes with label Person and property location with the name index_name and the given spatial.cartesian settings. The other index settings will have their default values.Point indexes only solve predicates involving POINT property values.



