
To truly grasp the nuances and potential challenges of the Lightning Network, it’s crucial to dive into the very heart of Bitcoin. One of the inherent constraints of the Bitcoin network lies in its architecture, where every transaction is required to fit into a newly mined block. Given that a new block is appended approximately every 10 minutes, this structure creates an inescapable bottleneck for transaction throughput, especially if the fundamental Bitcoin protocol remains untouched. Overall, we think that Bitcoin and the Lightning Network can deeply disrupt the logics in place in the legacy financial system. Programmable assets are very powerful tools that will reshape the standard for a better transparency and risk control. We have given each crypto dark web a ranking based on our comprehensive review of the features above.
Some chase banned goods—like a coder I met hunting censored PDFs—others love the mask it offers. Vendors price by risk; a rare pill might cost triple what’s on the street. Pills—legal or otherwise—top the charts; one vendor bragged about shipping oxy in hollowed-out books. Bitcoin and Monero roll here; I grabbed a cheap tool last Tuesday and had it by Friday. Cybercriminals on the dark web marketplace always look for new victims to target them with scams or infect their devices with malware, spyware, or adware. Thus, use the best antivirus software that protects against these online threats.
Beyond Tor: Other Dark Paths
Only the opening and closing of these channels are recorded on the blockchain, reducing congestion and lowering fees. This structure enables users to send and receive Bitcoin quickly and efficiently, making small, frequent transactions—like buying coffee or tipping online—feasible without overwhelming the main network. The collapse of Hydra Market in 2022, once responsible for over 80 percent of darknet market traffic and more than $5 billion in lifetime turnover, created a vacuum.
Secure Payments And Trusted Dаркнет Links For Smooth Deals
Nodes contain a full record of every Bitcoin transaction that has ever been made. More than half of all the nodes need to agree that each new transaction is valid before it can be added to the blockchain. Buying illegal substances, stolen merchandise, and counterfeit currency or goods online poses significant risks for both the buyer and the seller. Once the website is coded, the policies created, the admins ready, and the hosting secured, the site goes live on the TOR network. Buyers won’t come to the site if there’s nothing to buy, and sellers won’t come to the site if there’s no one to buy their products. Server admins will have to either make special agreements to get initial sellers on board, or supply products themselves to get things started.
- This integration paves the way for traders to execute smaller Bitcoin withdrawals swiftly and at reduced costs.
- When the attacker receives a payment, it starts a clock, routes the payment, and stops the clock when it receives the “receipt”.
- Encryption protects communication, and onion routing anonymizes all interactions, making tracing nearly impossible.
- In the case of mass-adoption, the lightning network can very well be used to process the transactions for a drug trafficking store-front.
- The LN can facilitate some transactions thanks to a feature called cross-chain atomic swaps, which were first described in 2013.
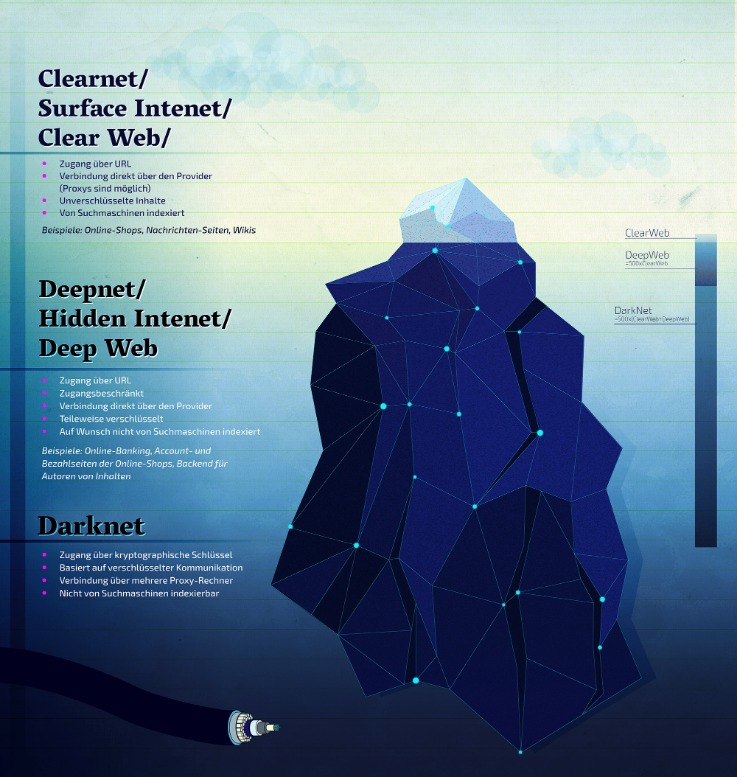
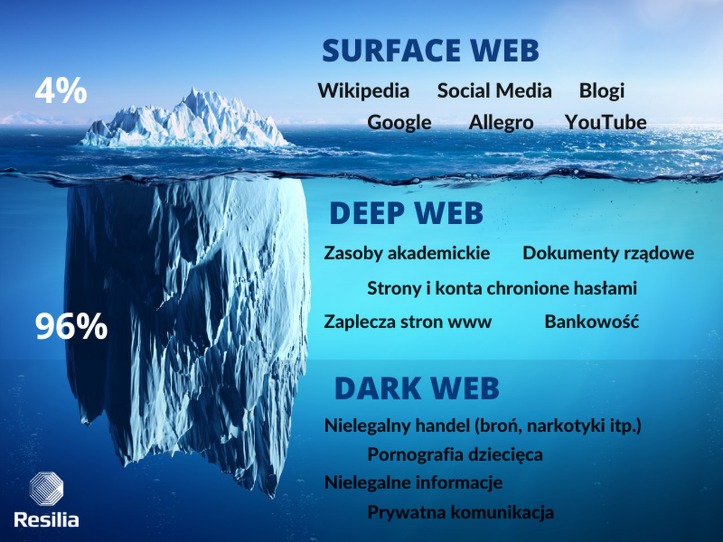
- The Deep Web includes all content not indexed by search engines.This isn’t necessarily illegal—it’s just private or restricted.
Unmasking The Dark Web Economy: Key Hubs And Cybersecurity Implications
On top of that, the Lightning Network is available 24/7, which means that transactions can be made at any time. By using the Lightning Network, donors can make donations to charities and non-profit organizations quickly and cheaply without having to pay high transaction fees. The Lightning Network can be used for remittances, which are money transfers from one country to another. With it, remittances can be made quickly and cheaply without the need for intermediaries such as banks or money transfer services.
Exploring The Use Cases Of Darknets & Dark Markets
Even users who access these platforms without intent to buy illegal items risk suspicion or investigation. Significant technological innovations and trends have reshaped dark-web marketplaces over recent years. In 2025, many platforms have adopted decentralized architectures, reducing single points of failure that previously made them vulnerable to law enforcement takedowns.
For example, an attacker could attempt to overload the network with invalid transactions or steal funds from payment channels. While the Lightning Network has security measures in place to prevent such attacks, it is still possible for them to occur. The ability to make cross-chain transactions has opened up new possibilities for businesses and developers, who can now create new products and services that rely on cross-chain transactions. It has the potential to revolutionize the way we think about payments and transactions, making it possible to use Bitcoin for a wide range of applications. The Lightning Network can be used to enable cross-chain transactions, allowing Bitcoin to be exchanged for other cryptocurrencies without the need for intermediaries.
Market Features
These markets leverage advanced encryption and decentralized infrastructure to ensure anonymity, making them preferred choices for buyers and sellers. Nexus stands out for its escrow system, which holds funds until delivery is confirmed, reducing fraud risks. Abacus offers a streamlined interface with multi-signature wallets, further enhancing trust. The Lightning Network has seen steady growth since its launch, with increasing adoption by individuals, developers, and businesses worldwide. Major cryptocurrency exchanges like Kraken, OKX, and Bitfinex, as well as apps like Cash App and Strike, have integrated Lightning to enable faster and cheaper Bitcoin transactions. Thousands of active nodes and tens of thousands of open payment channels now support the network, handling millions of dollars in capacity.
Darknet Marketplaces (DNMs) And How They’re Accessed
Once the buyer confirms satisfaction, the funds are released to the seller. In response, cybersecurity professionals, law enforcement agencies, and policymakers around the world are working to combat this growing menace. They employ various techniques, such as tracking and infiltrating dark markets, developing advanced threat intelligence, and enhancing international cooperation.
A second-layer protocol that is designed to solve Bitcoin’s scalability problem by allowing transactions to be processed more quickly. As some nodes accumulate many connections and large amounts of liquidity, they begin to act like hubs—similar to traditional financial intermediaries. This undermines Bitcoin’s goal of decentralization and could lead to single points of failure or influence if left unchecked. Physical merchants can integrate Lightning payments into their POS terminals, offering customers a fast and modern payment alternative without relying on cards or cash. To turn it on, just go to the “Settings” and then the “Tools” section of the NordVPN app and activate “Dark Web Monitoring.” In the end, it’s all about staying one step ahead.

Platforms like Nexus and Abacus dominate due to their streamlined interfaces and robust encryption, ensuring transactions remain private. Buyers benefit from competitive pricing, often lower than street markets, while vendors maintain high standards to secure positive feedback. Modern darknet markets prioritize user-friendly interfaces, resembling mainstream e-commerce sites. Features like encrypted messaging, auto-generated PGP keys, and built-in coin tumblers streamline the shopping experience. Markets such as Archetyp and Incognito have optimized their platforms for mobile Tor access, catering to users who prefer convenience. From at least April 2021 until May 2023, McDonald and others conspired to sell fentanyl and cocaine via multiple darknet marketplaces.
Dispute resolution is faster, with blockchain-based evidence logs for contested orders. The shift to self-executing smart contracts on platforms like Abacus minimizes human intervention, further securing deals. Blockchain-based indexing, like ZeroNet, allows peer-to-peer link sharing without centralized points of failure. Buyers prioritize markets with multisig escrow and PGP-verified admins, features now standard in top-tier platforms.
This is known as the “funding transaction” and is broadcasted (visible) to the blockchain. However, when she approaches the counter to pay, she is advised by the barista that her payment needs to be confirmed on the blockchain before her coffee is prepared. From micropayments for digital content to enhancing the functionality of decentralized finance (DeFi) applications, the network is expanding its utility beyond simple transactions. These innovative applications are attracting attention and investment in the ecosystem, fostering further growth. Moreover, transaction costs are greatly reduced when using the Lightning Network.
Cryptocurrency Transactions
Markets now integrate multi-signature escrow systems, reducing fraud risks while maintaining trust between buyers and vendors. Darknet markets in 2025 have refined their security protocols and vendor reputation systems, making drug transactions safer and more reliable than ever. Multi-signature escrow, end-to-end encryption, and mandatory PGP communication are now standard, reducing risks for both buyers and sellers. Markets like AlphaBay Reloaded and Incognito use automated dispute resolution and decentralized hosting to minimize downtime and exit scams. DarkMatter is a darknet marketplace built for those who demand both power and discretion.



