
WeTheNorth has a strong community vibe, with an active forum where users interact and share updates. It has a search option to let you find local and international products and services on the dark web. A lot of vendors from all over the world are registered here, offering an extensive range of products, including digital services, security tools, and other equipment.
First, Install A Reliable VPN
This enables individuals to form groups and only share content in a highly anonymous network of darknet users who they know. The core principle of the Tor network was first developed by U.S. Naval Research Laboratory mathematicians and computer scientists in the mid-1990s.
- If you want to be untraceable and undetectable, connecting to the dark web via the Tor browser is a major step towards that, but not the only step you’ll need.
- Besides ever increasing hosting costs, the site will have to contend with authorities, attacks from hackers, and the occasional disgruntled market administrator.
- The use of the dark web raises suspicion as it shows there is something you want to do privately.
- There are some things that you can’t find on the surface internet but are available in the darknet markets.
- That means website operators and third parties can’t track your online activity when you use Torch.
It has a reputation for being fast and effective, though the content it indexes varies widely in quality and legality. On some cybercriminal forums, the Hydra related topics were closed by moderators. We deliver contextualized, actionable intelligence through our dedicated platform or API integration, ensuring that you can respond effectively to darknet threats. The Dark Web and Darknets offer valuable spaces if you value privacy, freedom of speech, or research security technologies.If you misuse them, the consequences can be severe. Darknet tools have real value in privacy-focused, humanitarian, and journalistic efforts. Unlike the Deep Web, Darknets are intentionally hidden and designed to preserve privacy and anonymity.
This highly popular English-language market sold all varieties of narcotics. DNMs have a limited life and may be shutdown suddenly, leaving users with unfulfilled orders and sellers with no means of communication. To avoid immediate shutdown, the servers hosting DNMs must be in countries with lax legal regulations.
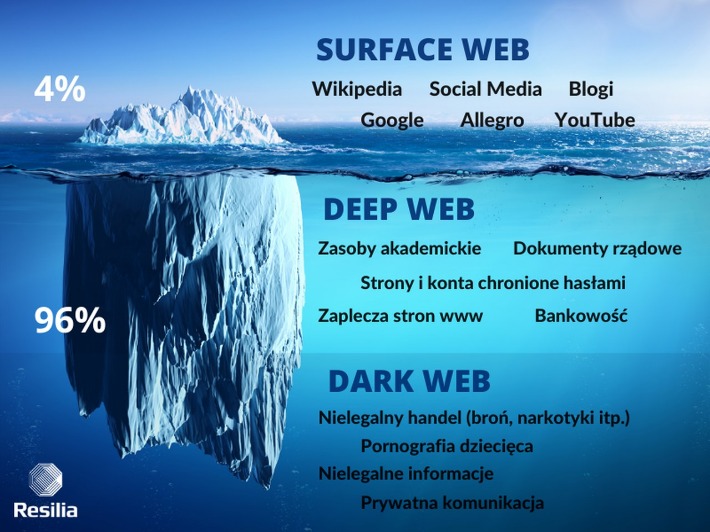
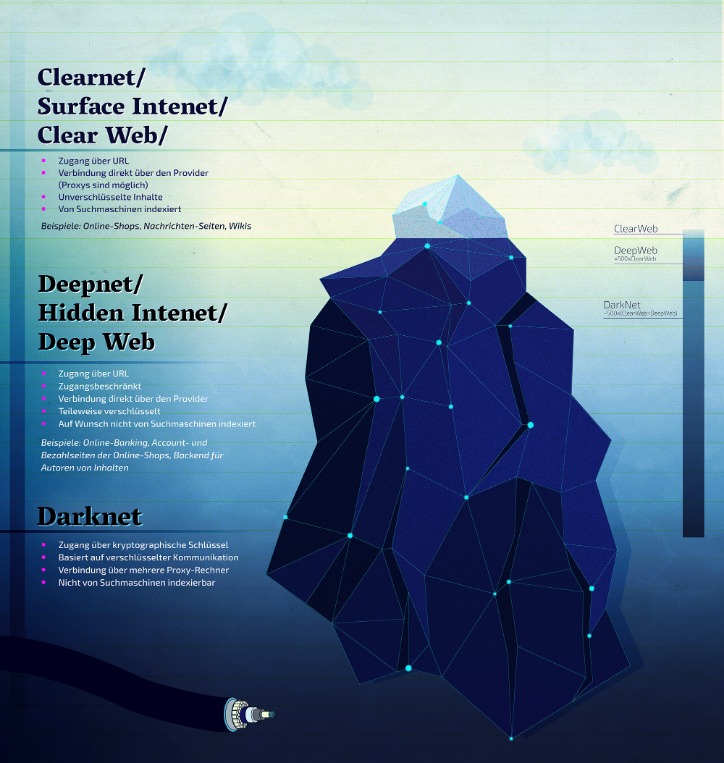
Regardless of the browser’s anonymity, it is still illegal to commit fraud or engage in any illegal activity on the dark web. According to a 2020 estimate conducted by Prey Project (a security service platform), 57% of the dark web is illegal. The dark web isn’t indexed by regular search engines and is known as a hotbed of criminal activity. While that’s sometimes true, it can also be used for ethical purposes. There are a lot of misconceptions about the dark web online and in popular media. When most people refer to the dark web, they are thinking about dark web/darknet marketplaces (DNMs).
Additional Tips On How To Stay Safe While Accessing The Dark Web

Some alternative links are available, providing access to the marketplace. It’s recommended not to use new alternative links as they could just be planned exit scams. The marketplace has a pleasant, user-friendly interface built from the ground up. Its interface makes it easy to identify clone websites and ensures that users always use the authentic site.
Paying With Monero: A Quick Rundown
Internet providers and websites can detect when Tor is being used because Tor node IPs are public. Although websites can’t identify you and ISPs can’t decrypt your internet traffic, they can see that Tor is being used. Your ISP, and possibly the authorities, may decide to start monitoring your activity more closely to look for threats or illegal activity. That’s why we always recommend using a VPN over Tor—even if you feel you have nothing to hide.
Types Of Dark Web Sites (and What Really Goes On There)
You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. The system is designed to provide enhanced security and privacy features. Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity. The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address.
Tor And The Onion Browser

If your information surfaces in these murky depths, there’s very little you can do – but knowing the risks involved is a first step toward defence. It’s a lifeline for activists, whistleblowers and journalists seeking safe spaces to connect and speak freely. Social platforms buzz with anonymous conversations, even as law enforcement hunts through digital shadows to crack down on criminal rings. Tor’s elaborate onion routing technique makes web tracking extremely difficult, but it’s still possible for third parties to spy on certain aspects of your web activity. And it hides your IP address from hackers, your internet service provider (ISP), and even government spies. You can download the desktop version of the Tor browser directly from the Tor project’s website.
How To Access onion Sites Safely
You won’t be able to search the dark web with a regular browser (such as Chrome or Firefox). Besides, your online activity on such browsers is visible to your ISP unless you connect to a VPN service. There are a few reasons why the dark web isn’t stopped or shut down. First, it’s difficult to track and monitor activity on the dark web since much of it is encrypted. The Tor network was created by the US military in the 1990s for anonymous communication between spies over the internet. That effort was never fully realized, but the US military published the code under a free license in 2004.
The Best Dark Web Markets To Consider In 2025

It offers outstanding privacy features and is currently available at a discounted rate. Second, shutting down or controlling access to the dark web would be a huge undertaking and could have unintended consequences. Finally, many people consider the dark web a necessary tool for privacy and freedom of speech. In fact, there is an entire section of the dark web dedicated to pornographic content. However, it is important to note that not all of this content is legal.
- It’s designed as an environment to elude detection, where site owners and visitors hide their identities.
- One of the great things about Tor is that it can be used to access both the dark and surface web.
- Use it to link your GitHub account, Twitter, Bitcoin address, and Facebook.
- Google only indexes websites on the open web (freely accessible and public), while dark web sites use .onion domains that are not visible to traditional search engines.
How To Access Darknet Markets Safely
Tor browser apps for Android or iOS are available on Google Play and the App Store. Once you have Tor or another dark web browser, use one of the top unfiltered search engines to help you find the dark web content you’re looking for. The Hidden Wiki isn’t completely unrestricted, because it uses filters to block many of the scam sites found on the dark web.
The legality depends on your activities and your country’s specific laws regarding darknet use. Transactions within dark markets predominantly involve cryptocurrencies like Bitcoin, Monero, or Ethereum. These digital currencies provide a degree of anonymity, as transactions are recorded on a public ledger but do not directly link users to their real-world identities. Darknets and dark markets have fueled the growth of cybercrime, provided a marketplace for cyber threats, and expanded the attack surface for malicious actors.
While these hidden networks can be used for legitimate purposes, they are equally significant as vectors for cybercrime and illicit activities. Personal and financial data are commonly sold on dark markets, facilitating identity theft and fraudulent activities. The significance here lies in the potential damage to individuals and businesses. Companies must implement strong data security measures, employ encryption, and monitor for data breaches to protect customer and employee information.



