
Some believe STYX is the OG darknet market when it comes to financial crimes. It trades in hacked bank accounts, stolen credit card information, and other services that facilitate cryptocurrency laundering. Therefore, it’s clear that as long as there’s demand and supply of illegal products, the darknet markets are going nowhere anytime soon, no matter the number of times law enforcement takes them down. Ideal marketplaces support anonymous browsing through networks like Tor and I2P, utilize privacy-focused cryptocurrencies such as Monero, and implement measures to prevent tracking and transaction tracing. Platforms that provide clear guidelines for maintaining operational security (OpSec) and offer built-in tools for data obfuscation are especially favored. Still, even with these crackdowns and better defenses, dark web markets just keep coming back.
Reducing Personal Data Risks
Abacus Market quickly rose to prominence by attracting former AlphaBay users and providing a comprehensive platform for a wide range of illicit activities. Darknets and dark markets have fueled the growth of cybercrime, provided a marketplace for cyber threats, and expanded the attack surface for malicious actors. For directed betweenness centrality, paths must follow the direction of the edges, while undirected betweenness can follow edges in either direction. Like for harmonic closeness centrality, the weighted variants use the inverse of the edge weights during shortest path computation, such that stronger connections equate to shorter distances. As direction and weighting can have a large impact on the probability of lying on a shortest path, we use the directed weighted betweenness in this study. We note that where the interpretation of paths was unclear for harmonic closeness centrality, this is less of an issue for betweenness centrality.
That way, they aim to create secure forums and limit outsiders like law enforcement. Likewise, law enforcement agencies each day continue to fine-tune their strategies to get past these networks. BidenCash is another latest marketplace that started in 2022, and is now home to sensitive financial data transactions. This is where cybercriminals go to buy and sell things like stolen credit card numbers, personally identifiable information (PII), and even SSH login details.
Windows OPSEC: Disabling Network Tracking
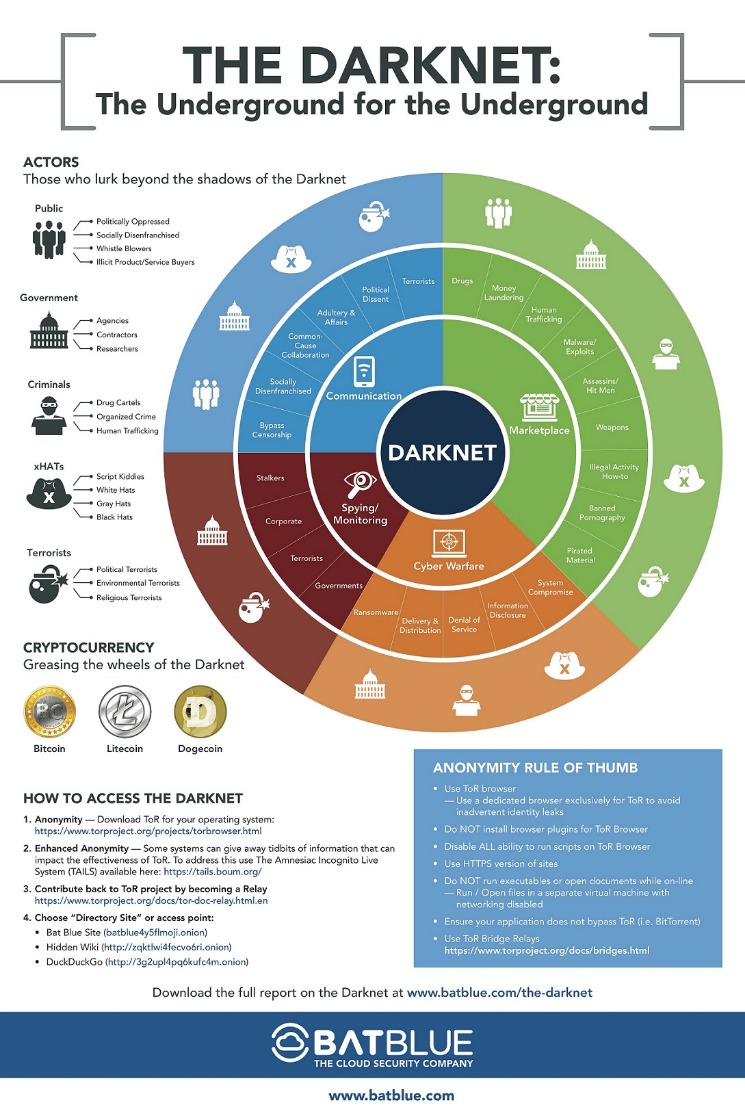
While these marketplaces continue to serve legitimate purposes, such as enabling secure communication and privacy protection, they also remain hotspots for illicit activities and cybercrime. Technological advancements like AI-driven security, quantum-resistant encryption, and blockchain integration are reshaping the landscape, but simultaneously, global enforcement efforts grow more sophisticated and collaborative. Although dark-web marketplaces utilize technologies like Tor and I2P to enhance anonymity, these methods are not foolproof.

Finland Seizes Servers Of ‘Sipultie’ Dark Web Drugs Market
In Supplementary Material Section S4, we investigate the performance of the measures at different thresholds. We observe that for low false positive rates, up to around 20%, our findings hold. For higher false positive rates however, topic engagement clearly outperforms all other measures. However, given the limited resources of law enforcement, it is unlikely that such large user samples would ever be considered for investigation.
- These are all old and now trivial approaches that the CAPTCHA community has abandoned years ago.
- Due to its privacy-focused technology and popularity, Monero has become a cryptocurrency of choice for darknet markets in recent years.
- We note that where the interpretation of paths was unclear for harmonic closeness centrality, this is less of an issue for betweenness centrality.
- This is the part of the internet known as the dark web, and it’s accessible via mainstream search engines such as Google.
- The results highlight that the same measures are almost as effective at recognizing those that will do well in the future.
Stellar Targets $070, Dogecoin Risks $020 Drop While BlockDAG’s 2049% Bonus Till TOKEN2049 Steals The Show
On these marketplaces, they’re listed, sold, and promoted just like items on any e-commerce site. They suffer losses such as identity theft, financial loss, and emotional distress due to damage to their personal and professional lives. They really don’t care about the loss and dilemma of the victims whose data has been stolen. For example, an insider or factory employee might quietly slip away with an unmarked gun and sell it online. Once it lands on a darknet marketplace, it becomes part of the illegal weapons trade.
Install OnionScan (`go Get Githubcom/s-rah/onionscan`)
Some things, like medical records, driver’s licenses, and passport information. The consequences can be lethal to those whose data is stolen, like identity theft, emotional distress, and even financial loss. We deliver contextualized, actionable intelligence through our dedicated platform or API integration, ensuring that you can respond effectively to darknet threats. Ethically, they must minimize harm, responsibly handle any stolen or sensitive data (often notifying victims or law enforcement), avoid entrapment, and maintain research integrity. They’re tightening security and carefully screening anyone who wants to join. This vetting process helps keep the community “clean” from spies, law enforcement, or anyone who might pose a risk.
Ready To Explore Web Data At Scale?
- The re-emergence of Black Ops underscores the need for adaptive cybersecurity strategies.
- Transactions can still be traced back to individuals through blockchain analysis.
- MFA is often optional when browsing listings but mandatory for purchasing items.
- And yet, what Monero might be best known for in the general public is its now-common usage in illicit transactions.
- Since then, there has been some speculation as to which market will take the number one spot.
- Of course, the promise of secrecy and unfiltered access might lure you in, but those same features are what make the environment so risky.
AI-powered blockchain analysis tools can trace Bitcoin and other cryptocurrency transactions linked to illegal activities. AI-powered tools use machine learning, pattern recognition, and NLP to analyze darknet forums, detect suspicious activities, and track stolen credentials. An encrypted operating system adds another layer of protection by safeguarding your data, even if your device is lost, stolen, or compromised. Avoid using mainstream operating systems like Windows or macOS for this purpose, as they may not provide the level of security required for dark web activities. Instead, opt for privacy-focused systems designed to enhance anonymity and protect sensitive information. TorHunter provides detailed guides and tutorials to help you implement these measures effectively.
AI can analyze transaction patterns, behavior, and linguistic traits to identify darknet users, but complete de-anonymization remains challenging. Cybercriminals are now using AI themselves to evade detection, making it necessary for cybersecurity experts to continuously enhance AI security systems. AWEX also provides cash services in Moscow and Dubai, allowing customers to load funds onto Sberbank and Alfa-Bank credit cards, two OFAC-designated Russian banks. The development community that supports Monero is broken into various workgroups with roles that include infrastructure, community, development, regulatory compliance and more. Ehrenhofer’s Monero Space workgroup, for example, provides a number of services to the coin’s community.
Ethereum Futures Hit Record OI, BitMine Targets 5% Of ETH Supply
At the same time, they are increasingly becoming a serious challenge for both scholars and law enforcement agencies. Additionally, international law enforcement agencies have been collaborating closely to dismantle these illicit marketplaces. Joint operations and information sharing between agencies such as Interpol and Europol have led to significant successes in shutting down major darknet platforms.

Overall, Abacus Market distinguishes itself through rigorous security measures, effective moderation policies, and a strong emphasis on protecting user privacy. Despite minor accessibility inconveniences, these strengths have solidified its position among the top dark-web marketplaces in 2025. The best marketplaces in 2025 cater to diverse needs, offering a broad spectrum of products ranging from privacy-enhancing software, digital documents, and cryptocurrency exchanges to more sensitive or controversial goods. Marketplaces that maintain strict moderation policies—banning excessively harmful or exploitative products—also gain popularity among more ethically minded users. However, you can trace its roots to the development of technologies like the Tor network or Freenet. In March 2000, an Irish grad student named Ian Clarke created the software application, Freenet.
After all, the resources required to investigate even 20% of users would likely exceed those available to law enforcement. Additionally, we find that topic engagement is the best measure for predicting vendors, regardless of their level of success. In the Results section we shortly describe the dataset and measures used before reporting on our results. The results and their implications for law enforcement are discussed in the Discussion section. Finally, the “Methods” section provides more in-depth descriptions on the dataset and network extraction as well as the activity indicators, network measures, and evaluation metrics used in this work.
A Brief Overview & History Of Darknets & Dark Markets
It’s known for its strong security features (like a trusted escrow system, PGP two-factor authentication) and anonymity. Contrary to popular belief, Bitcoin and other cryptocurrencies are not the holy grail of untraceable transactions on the darknet. While they offer a certain level of anonymity, it is important to note that their use in darknet markets does not guarantee complete invisibility.



