Notably, Abacus explicitly forbids highly dangerous goods, including weapons, explosives, and exploitative material, which has helped maintain a relatively favorable reputation among its user base. The alleged owners, Tal Prihar, 37, and Michael Phan, 34, both from Israel, were arrested Monday, Prihar in France and Phan in Israel, where they remain in custody. They each face a single count of money laundering conspiracy in the U.S. Immigration and Customs Enforcement’s Homeland Security Investigations (HSI), Department of Defense (DOD), and FinCEN. According to the indictment, between October 2013 until the date of the indictment, Tal Prihar and his co-conspirator Michael Phan allegedly owned and operated DDW, hosted at
Dark Web Tools And Services
By 2017, however, AlphaBay was shut down by law enforcement as well. Two of the biggest digital black markets both seem to be disappearing. The former has halted trading altogether, while the latter appears to be confiscating user funds. However, many are used for illegal activity and onion websites are often popular hangouts for cybercriminals and scammers. Using common sense like avoiding clicking on shady links or download buttons, sticking to known sites and adding a VPN for an extra layer of protection, you should be fine. It’s a bit of a contradiction to talk about search engines for dark web sites because, by definition, these are not sites that get indexed by traditional search engines.

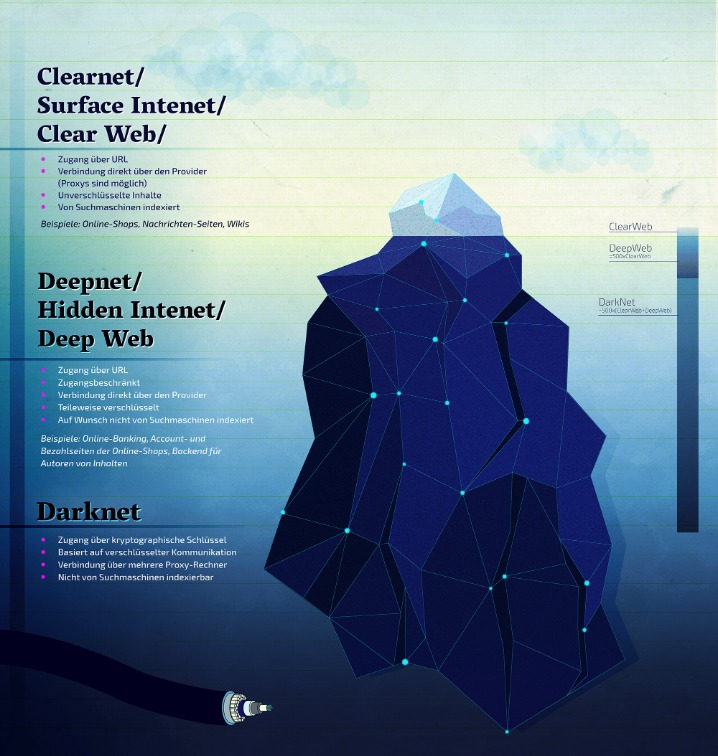
Founded in 2014, BriansClub remains one of the oldest and most infamous dark web markets for stolen credit cards, fullz (complete identity kits), and dumps. The most common darknet software is the free and open-source Tor, short for the Onion Router. The software was developed in the mid-1990s to protect U.S. intelligence communications online and is used in conjunction with virtual private networks (VPNs). Tor software, in conjunction with the user’s preferred VPN, conceals the user’s location and IP address and is implemented through layers of encryption, akin to the layers of an onion, from which the service derives its name. While some competing darknet softwares are similar to Tor browsers, they typically exist for different purposes. For example, the network dn42 exists to help users form connections and networks rather than to preserve user anonymity.
Dark Web Search Engine

According to Deep Dot Web, the marketplace was initially hard to reach, most likely due to ongoing distributed denial of service (DDoS) attacks on the website. The attacks appeared to exploit a weakness in the anonymizing Tor browser — needed to access the website — which made the cost of such an attack relatively low. This sequence offers less anonymity because your real IP address is still partially exposed along the Tor path. Plus, it’s slower since your data travels through the same four steps – entry node, relay node, exit node, and then the VPN server.
Dark Web Links: The Best onion And Tor Sites In 2025
Darknet markets, in particular, have gained attention for their role in facilitating the exchange of illicit goods and services. Despite their controversial nature, these marketplaces continue to evolve, offering a glimpse into the darker side of online commerce. As cyber threat intelligence professionals monitor these markets, they gain insights into emerging threats and malicious activities that can impact organizations and individuals. In addition to counterfeit merchandise, MGM Grand Market offers access to stolen credit card information, compromised bank accounts, and other financial fraud-related services.
Cybersecurity Workforce Trends In 2025 – Skills Gap, Diversity And SOC Readiness
There’s also a search bar that you can use to search for any particular product or vendor. The browser uses onion routing technology to route the internet traffic through multiple relay nodes that provide layered encryption. The layers of encryption hide your data and activity from snooping eyes. The market is known for its extensive product listings and reputation system that helps buyers evaluate the reliability of vendors. Bohemia accepts Monero and Bitcoin as payment methods and places a strong emphasis on protecting user anonymity through PGP encryption.
- Ratings are easily manipulated, and even sellers with long track records have been known to suddenly disappear with their customers’ crypto-coins, only to set up shop later under a different alias.
- Buyers and sellers frequently face risks from malicious actors posing as legitimate vendors or customers, potentially leading to financial loss or exposure of sensitive personal information.
- Explore these alternatives to keep up with the latest developments—securely and responsibly.
- Just Another Library is one such service, with a wealth of books covering computer programming, science, and niche hobbies (sailors’ knots, anyone?).
- The Cannabis Growers and Merchants Cooperative (CGMC) is a private, invite-only marketplace.
One of the most common types of illicit goods is stolen login credentials, often collected from data breaches. These “credential dumps” allow criminals to access online accounts, steal identities, and commit fraud. Dark web markets work much like regular e-commerce websites but with extra layers of anonymity and encryption.
Stick to cryptocurrency, avoid downloading anything, and don’t share any personal info. If you ever decide to explore the dark web, protecting your identity is crucial. Most people start by using the Tor Browser, which hides your IP address. There’s also a privacy angle—some users live in countries with censorship or surveillance, and the dark web gives them a space to communicate or access information more freely. But don’t expect the dark web’s downtime to last, says Roman Sannikov, an analyst at security firm Recorded Future.
Dark Web Ammunition Purchase: Scottish Software Engineer Got Five Years Jail
Anyone considering engaging with these platforms must carefully evaluate potential consequences, exercise stringent security practices, and remain vigilant to minimize exposure to these significant hazards. Ideal marketplaces support anonymous browsing through networks like Tor and I2P, utilize privacy-focused cryptocurrencies such as Monero, and implement measures to prevent tracking and transaction tracing. Platforms that provide clear guidelines for maintaining operational security (OpSec) and offer built-in tools for data obfuscation are especially favored. The website also provided access to marketplaces for firearms, including assault rifles, and for malicious software and hacking tools. This case was brought in conjunction with the Hi-Tech Organized Crime Unit, Joint Criminal Opioid and Darknet Enforcement (J-CODE) Team.
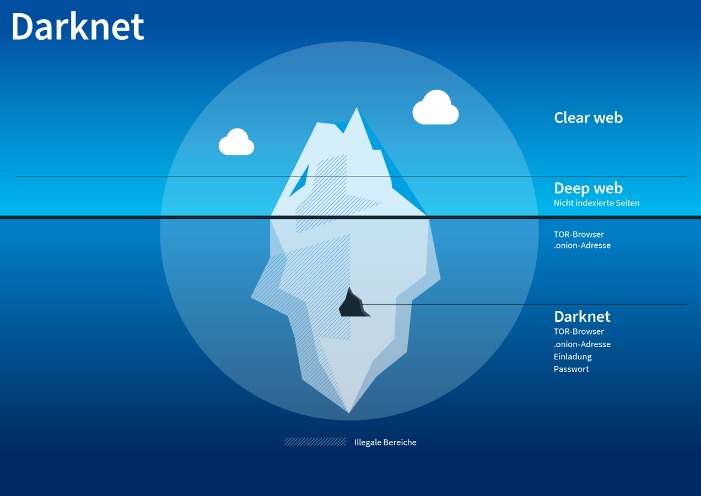
Naval Research Laboratory in the mid-1990s and later released to the public. Tor, short for “The Onion Router,” routes internet traffic through a global network of volunteer-operated servers to anonymize a user’s online activity. This technology initially had noble intentions, aiming to protect activists, whistleblowers, and individuals in repressive regimes. However, it soon became a double-edged sword as malicious actors began to exploit its capabilities for illicit purposes. Ahmia, which received backing from the TOR project in 2014, boasts top-tier filters.
Best Free VPNs For The Dark Web In 2025: Secure & Fast
The government has shut down major darknet drug marketplaces in the past, but they were quickly replaced by new ones. In July 2017, federal authorities in the U.S. shut down the AlphaBay and Hansa drug markets. But within days another darknet market had already picked up most of the listings, highlighting the challenge authorities face.
Bestmixer.io was, of course, only one of many coin mixing solutions for Bitcoin to begin with, and several darknet markets are also accepting privacy coin Monero (XMR), which effectively “mixes” every transaction by default. Hansa, however, turned out to have already been taken over by Dutch police. In what was called “Operation Bayonet,” new users from AlphaBay were trapped into entering passwords and more potentially identifying information in the compromised version of the Hansa website. After several weeks, Hansa was finally closed down as well, meaning the two biggest darknet markets were taken down within a span of several weeks. Anonymity of the dark web is one of the main draws for using onion sites, and most dark web links use a “.onion” domain. This is usually due to the sensitive nature of the businesses or services they offer.
The dark web hosts a variety of illegal activities, many of which fuel cybercrime and real-world harm. The latest round of shutdowns and arrests resulted from a broad scale cooperation between law enforcement agencies across different jurisdictions. Dark web search engines exist, but even the best are challenged to keep up with the constantly shifting landscape. The experience is reminiscent of searching the web in the late 1990s.
Indicators Of Compromise In Threat Intelligence
For each dark marketplace m that was shut down, we identify users who started trading on another coexisting marketplace \(m’\) after the closure of m. If a user was trading on both marketplaces m and \(m’\) before the closure of marketplace m, the user is not labelled as a migrant to marketplace \(m’\). In fact, migration was observed37 after the closure of the AlphaBay marketplace when other marketplaces, namely Hansa and Dream Market, experienced an abnormal spike in activity.