
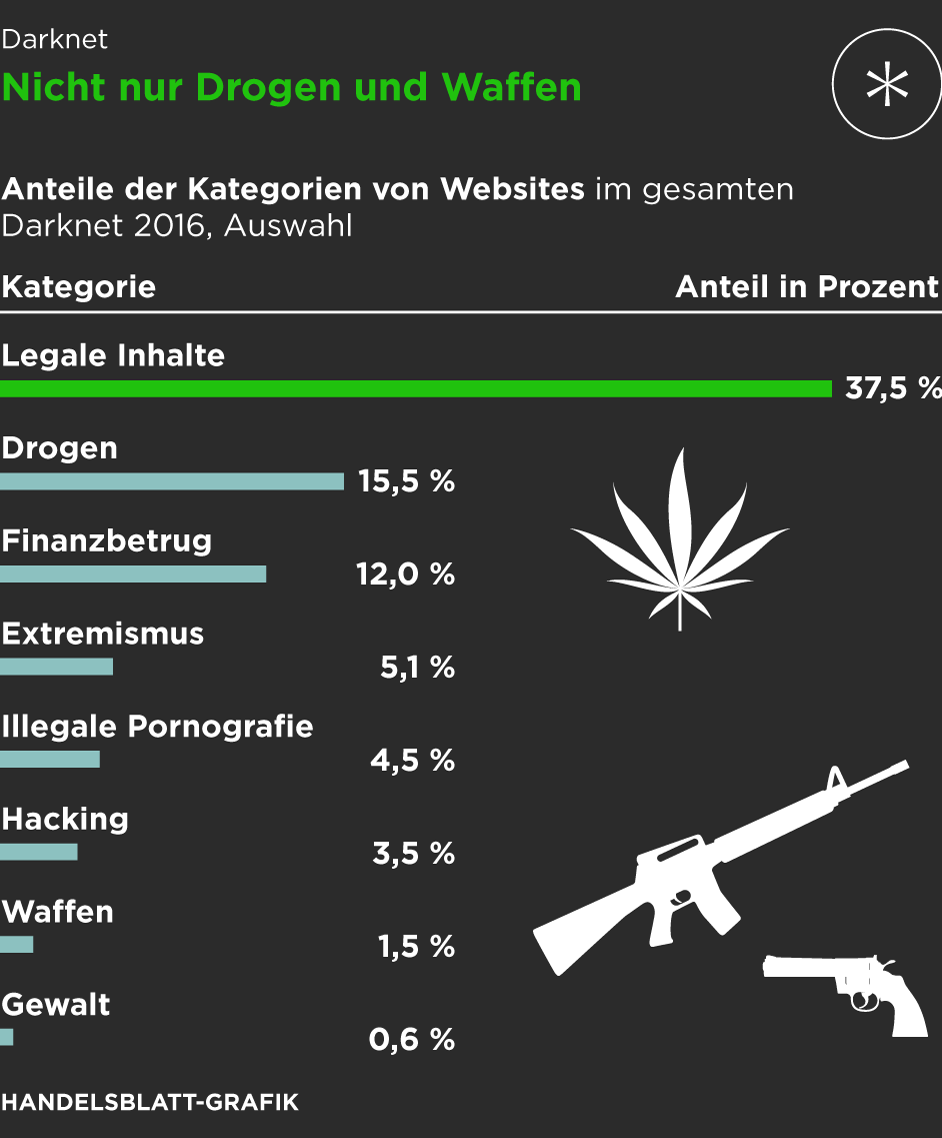
As long as people want to buy and sell illegal stuff online, be it stolen data, narcotics, drugs, or malware, these markets will keep resurfacing, no matter how many times authorities take them down. Many people go to the dark web to buy things they can’t find elsewhere, but what if what you’re buying is also trying to harm you? Scammers on darknet markets claim to offer legit tools or services, but instead provide you with malicious software that can infect your device.
- Cryptocurrency offers several advantages on the dark web, from the transparency of blockchain technology to the encryption of transactions, ensuring a high level of privacy and anonymity.
- Launched in 2020, Cypher Marketplace sells fraudulent documents, stolen credit cards, fake IDs, and malware.
- This means that casinos must perform KYC and source of wealth checks on customers seeking to deposit large amounts.
- Activities on dark-web marketplaces are closely monitored by international law enforcement agencies.
- Other variations of extortion begin with the scammer using phishing techniques to take control of the victim’s Instagram profile.
- AI simplifies pattern recognition, and blockchain forensics leverages openness in trying to follow illegal transactions and construct lawful evidence.
Overcoming The Challenges Of Decentralized Cryptocurrencies
Analytics Insight is an award-winning tech news publication that delivers in-depth insights into the major technology trends that impact the markets. The content produced on this website is for educational purposes only and does not constitute investment advice or recommendation. Always conduct your own research or check with certified experts before investing, and be prepared for potential losses.
Trump Media’s $64 Billion Crypto Push: What It Means For CRO, Politics, And The Future Of Crypto Adoption
Overall, dark-web marketplaces inherently involve substantial risk, and users must thoroughly understand these threats. Anyone considering engaging with these platforms must carefully evaluate potential consequences, exercise stringent security practices, and remain vigilant to minimize exposure to these significant hazards. Users must look for platforms employing robust encryption protocols, secure escrow services, and advanced anti-phishing measures. Additional layers, such as two-factor authentication (2FA), encrypted PGP messaging, and built-in wallet security, significantly enhance protection against theft and hacking. Overall, dark-web marketplaces in 2025 are more sophisticated, secure, and resilient than ever before, evolving rapidly in response to both technological advancements and intensified scrutiny from global law enforcement agencies. Tor2door’s been a standout since 2020—over 20,000 listings and a custom-built site that’s not some cookie-cutter junk.
Regulators, banks, and blockchain developers must work together to counter evolving laundering tactics while maintaining the integrity of digital finance. A proactive approach can help balance security with the continued growth of the crypto ecosystem. Criminals employ layering and structuring methods to conceal their illicit Bitcoin transactions, which are hard to track and regulate. By breaking large sums into smaller transfers and leveraging multiple exchanges, they evade regulatory scrutiny. These methods exploit gaps in compliance frameworks, complicating efforts to track and prevent financial crimes.
Tordex Search Engine
Accessing them may require .onion links and the Tor browser, but caution is advised due to legality and cybersecurity risks. Some markets are invite-only or have strict registration rules to keep out scammers and law enforcement. One of the most common is the exit scam, where a marketplace suddenly disappears and takes everyone’s money with it. Ransomware and cryptocurrency-based crimes saw a significant increase in 2023, with a nearly $176 million rise compared to 2022. In 2019, there were approximately 8,400 active sites on the dark web, selling thousands of products and services daily. As of 2020, nearly 57% of the dark web was estimated to contain illegal content, including violence and extremist platforms.
Ponzi And Pyramid Schemes In The Digital Era
They take BTC and Monero, and the site’s got a sharp, modern look—vendor profiles are loaded with ratings and reviews, easy to skim. What’s dope is their forums—real talk, not just noise—building trust like Telegram’s side hustle vibe. For 2025, they’re hyping a peer-to-peer escrow twist—could cut out middlemen and shake up how deals flow, which I’m stoked to see play out. It’s not as massive as Abacus, but quality’s on point—vendors deliver, and the community’s buzzing on Dread about it. I’ve poked around; it’s not overwhelming, just a tight selection that works—think curated over chaotic.
The Rise Of Crypto Fraud

The ASAP is a moderate design marketplace on the dark web that offers helpful tools like mandatory PGP encryption and two-factor authentication for a safe browsing experience. Like other marketplaces, ASAP Market also requires you to register for an account. If any user is found not complying with the law, strict and immediate action will be taken against them. It uses PGP encryption to protect sensitive data and messages, and accepts payments via Monera and Bitcoins to keep you anonymous on this marketplace.
Transactions are encrypted and recorded on a public ledger called the blockchain, which makes it difficult for hackers to manipulate or steal funds. Apart from the dark web markets that are operating online today, some raided platforms influenced many markets. Active for a decade since 2014, it is a widely used credit card shop used to source stolen credit card information such as dumps, CVVs, Wholesale Accounts. It maintains a very strict level of user verification and integration with an official Telegram account to provide real-time updates to users.
- Monero and Zcash are known for their strong privacy features, with Monero in particular being designed to provide untraceable transactions.
- Darknet marketplaces face numerous challenges that can lead to their shutdown.
- It automatically routes all the traffic through the Tor Network, allowing you to stay anonymous.
- However, blockchain transparency allows law enforcement to trace illicit transactions, leading to asset freezes and sanctions on facilitators.
- Then, we investigate both market star-graphs and user-to-user networks, and highlight the importance of a new class of users, namely ‘multihomers’, who operate on multiple marketplaces concurrently.
- Regulators, banks, and blockchain developers must work together to counter evolving laundering tactics while maintaining the integrity of digital finance.
Surge In New Scams As Pig Butchering Dominates
Despite using a VPN, there’s always a risk of the VPN leaking your IP address through DNS or WebRTC leaks or misconfigurations when on a dark web forum or marketplace. Therefore, you must run an IP leak test to ensure that the VPN is working completely fine and is not risking your digital security. In 2013, the FBI shut down the Silk Road, but it was later relaunched in 2014 with the new name of Silk Road 2.0, but the German authorities shut it down in the same year. Other than the Silk Road 2.0, similar marketplaces also emerged, but they all went down sooner or later. Tor2door Market is among the largest dark net shops you must visit in 2025 if you’ve decided to visit such sites.
For FinCEN’s recent alert identifying red flags on potential Russian sanctions evasion attempts, including through the use of cryptocurrency, see here. A Canadian market established in 2021, WTN offers over 9,000 products, including narcotics, fake goods, and digital services. It operates in both French and English and has built a reputation for ease-of-use. Using TAILS is yet another security measure that protects your online identity on the dark web. It is a specific Debian-based version of Linux software that leaves no traces of the user activity or the operating system on the computer. It uses the Tor network because it is a popular network that helps to circumvent censorship and online surveillance.

We review and list tools and products without bias, regardless of potential commissions. This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacySavvy.com page. However, it has a sneak peek, easy guide steps, and/or a quick list providing quick in-page navigations and easily-found answers if desired. Notably, Abacus explicitly forbids highly dangerous goods, including weapons, explosives, and exploitative material, which has helped maintain a relatively favorable reputation among its user base. We’re back with another video in our Webz Insider video series on everything web data.
The result is a time series of lists of sellers and buyers for each period and for each market and the U2U network. Buyers simultaneously active on multiple markets also play the role of connectors in the ecosystem. Therefore, we analyse the temporal network where nodes are the active markets and an edge between the nodes represents the number of multibuyers between them, what we henceforth call the multibuyer network. The structural change seen in the multiseller network is not observed in the multibuyer network, as show in Fig. The evolution of the multibuyer network follows a similar pattern to the multiseller network until 2015, despite a stronger polarization around Hydra instead of AlphaBay during 2017.
Illicit Commerce Scams
In 2022, Portugal became among the first countries to allow the sale of a house using crypto. Most high-value real-world transactions involving crypto require KYC and source of wealth checks, which poses challenges for criminals. However, there remain myriad ways for illicit actors to evade such guardrails – often through the use of shell companies and cybercrime services. In 2021, SUEX, a Russian-language OTC broker, was sanctioned by OFAC for facilitating financial transactions for ransomware actors. Cryptocurrency-based gambling platforms make it difficult to trace funds through the service. This means that casinos must perform KYC and source of wealth checks on customers seeking to deposit large amounts.
STYX Market, for example, concentrates on financial crimes, offering access to hacked bank accounts, forged documents, and money laundering services. Other platforms concentrate solely on narcotics, counterfeit items, or stolen digital identities. This specialization allows vendors to cater to targeted buyers and refine their offerings. With law enforcement agencies improving their ability to track Bitcoin (BTC) transactions, darknet market operators and vendors are moving to Monero (XMR) as their cryptocurrency of choice. Many darknet marketplaces uses .onion links that are only visible in the Tor browser. Generally, darknet trading platforms apply the Escrow system to process the payments.
Furthermore, inexperienced users unfamiliar with secure cryptocurrency practices are particularly susceptible to these threats, risking the loss of their entire funds. Another notable trend is the rise of encrypted peer-to-peer (P2P) messaging systems integrated directly within marketplaces, providing secure communication channels between buyers and sellers. The integration of blockchain-based smart contracts is also becoming widespread, automating secure transactions and reducing the likelihood of fraud.



