Recent statistics indicate that the Tor network attracts approximately 2.7 million users each day. Originally designed to support free expression by safeguarding anonymity, Tor has become a nexus for criminal activity as well. One of the more intriguing developments in Tor usage is Germany surpassing the United States in user numbers for the first time. Analysts speculate that this shift may be tied to growing privacy concerns in Europe, alongside a broader cultural acceptance of encrypted communication tools. To access darknets, users typically need to download and configure the Tor Browser; a modified version of Mozilla Firefox that routes all traffic through the Tor network.
The tools and techniques used to keep these platforms running reveal vulnerabilities that businesses must guard against. Companies today face constant threats of data theft, intellectual property leaks, and other dangers that originate from the dark web. Launched in 2020, Cypher Marketplace sells fraudulent documents, stolen credit cards, fake IDs, and malware. Its emphasis on user anonymity and document forgery makes it a core tool for identity fraud.
Is It Illegal To Access The Dark Web?
Chainalysis data shows darknet marketplace revenue dropped post-Hydra seizure in 2022 but recovered to $2 billion in Bitcoin inflows during 2024 Darknet market BTC inflow drop and shift to Monero. Abacus alone represented nearly 5 per cent of total DNM revenue, underscoring the ongoing scale of underground commerce. Track and analyze darknet activities using our advanced cyber threat intelligence platform to stay ahead of emerging threats. Believe it or not, some dark web marketplaces have pretty advanced systems for building trust. Sellers often need to pay a deposit to prove they’re serious, and they build their reputation through positive reviews.
Silk Road And Early Markets
Transactions within dark markets predominantly involve cryptocurrencies like Bitcoin, Monero, or Ethereum. These digital currencies provide a degree of anonymity, as transactions are recorded on a public ledger but do not directly link users to their real-world identities. To purchase illicit goods or services, users deposit cryptocurrency into an escrow system or directly to the seller, and the cryptocurrency is held until the buyer confirms the satisfaction of the transaction. At KELA, we help you identify and mitigate risks by providing actionable intelligence from the darknet.
Explore The Products
TRM provides blockchain intelligence to help financial institutions, cryptocurrency businesses, and public agencies detect, investigate, and manage crypto-related fraud and financial crime. TRM’s risk management platform includes solutions for transaction monitoring and wallet screening, entity risk scoring – including VASP due diligence – and source and destination of funds tracing. These tools enable a rapidly growing cohort of organizations around the world to safely embrace cryptocurrency-related transactions, products, and partnerships. Dark web marketplaces are mostly hubs for illicit goods and activities, posing serious risks to users and the wider community. Flugsvamp 4.0 continues the lineage of Swedish-oriented darknet marketplaces. Catering mainly to a Scandinavian customer base, it lists a large selection of narcotics, counterfeit currency, and hacking tools.
Darknet Market Links ( Official )
- The vast array of illicit activities taking place within these digital realms has far-reaching consequences that extend beyond just the virtual realm.
- It offers access to hacked bank accounts, credit card data, and cryptocurrency laundering tools.
- Using DarkOwl Vision, the darknet, and darknet-adjacent sites DarkOwl analysts looked at vendors from Styx market to review the vendor’s footprints across the darknet.
- Dark web users rely on a combination of tools and networks to maintain their anonymity.
- Saheed Aremu passionately advocates for digital privacy and cybersecurity in the modern digital age.
If for any reason, you decide to visit these hidden corners of the web, ensure you at least study and understand the common traps. Getting familiar with the tactics scammers use will go a long way in helping you protect your online data and assets. In many countries, strict laws limit who can legally buy, own, or carry firearms. So when someone like a private buyer or criminal group can’t pass the background checks or get the right permits, they usually turn to the dark web to sidestep the rules and get armed without drawing attention.
However, its popularity increased shortly after the Bohemia, Hydra, and Monopoly markets were seized in early 2023. DarkOwl’s Vision database to date has over 19,000 results pertaining to Dark Empire Market. There is very little open-source information available to provide more information on the history of this site and its admins.

Risks And Vulnerabilities For Users
For each listing, the user has the option to get in contact with the seller directly to purchase the item. A “Get in Contact” button will either bring the user to a page with a chat box on the marketplace itself, or the user will be taken to a Telegram channel. The Telegram channels are a mix of bots or direct access to the sellers themselves. Some Telegram channels, such as the money laundering service “Verta”, are used by the sellers to make public their terms of service and to publish positive reviews of their services. Positive customer reviews are key to gaining trust in the darknet community.
OMG!OMG! Market: Across The Darknet
Dark Empire Market’s name is sometimes confused with Dark Market or Empire Market, which were both darknet markets which have been seized by law enforcement. Money laundering and financial crimes are major concerns in the context of navigating the threat landscape, with darknet markets playing a significant role. As an individual seeking belonging, it’s crucial to understand how money laundering techniques and regulatory frameworks impact our society. Additionally, you’ll delve into the potential risks posed by darknet markets in terms of public health and safety.
Future Trends And Predictions For Dark-Web Marketplaces Beyond 2025

The veracity of the information posted is unclear and could easily be falsified. DarkOwl analysts observed digital goods like bank accounts, Qiwi wallets, and SIMs for sale in addition to source code and software, such as Telegram bots. By embedding these standards into their security framework, organizations can minimize their exposure, fortify their defences and stay one step ahead of cybercriminals.
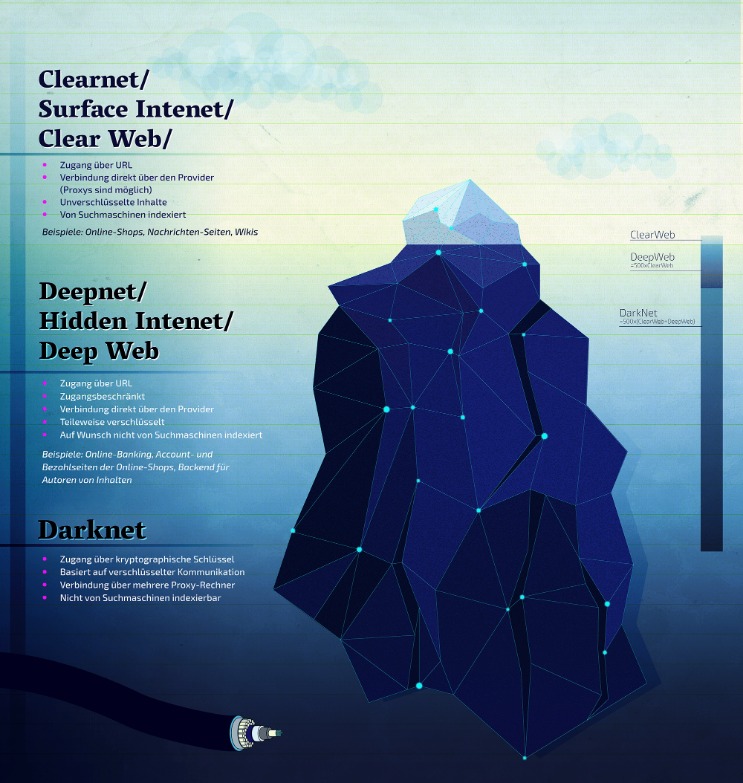
Since then, he has dedicated his career to writing extensively about crucial infosec, data privacy, and cybersecurity topics. When he’s not empowering PrivacySavvy’s readers to take control of their online security, Saheed enjoys distance running, playing chess, and exploring the latest open-source software advancements. However, you can trace its roots to the development of technologies like the Tor network or Freenet. In March 2000, an Irish grad student named Ian Clarke created the software application, Freenet.
They employ advanced technology to monitor darknet activities, focusing on identifying patterns and gathering evidence against criminals. In conclusion, the rise of darknet markets has had a profound impact on both our society and economy. Despite law enforcement agencies’ best efforts to combat this growing menace, the challenge remains daunting.

- Law enforcement raids represent one of the most common causes, as coordinated international operations often target servers, seize assets, and arrest site operators.
- Using his credentials, cybercriminals committed a variety of online fraud activity over the course of six months.
- The website has an interface and design similar to other dark web shops.
- As cyber threats grow more sophisticated, organizations are keeping a close watch on the dark web.
- To protect yourself and your organization from cyber threats, it’s important to follow cybersecurity best practices.
- The security level is set to ‘Standard’ by default, but you can change it to the ‘safest’ and enjoy more security while accessing the dark web.
It is considered very secure thanks to strict user validations and transparent payment and vendor review procedures. Its focus on financial fraud and high-value transactions has attracted a dedicated user base, contributing to its growing reputation and market value. STYX Market focuses specifically on financial fraud, making it a go-to destination for cybercriminals engaged in this activity. In the wake of recent headlines announcing actions against Hydra Marketplace by the U.S. and German governments, darknet markets have made an ironic entrance into the spotlight. Even passive activity on these sites can contribute to criminal networks.
Abacus Market is one of the newer darknet marketplaces that quickly filled the gap left by AlphaBay’s takedown. It hosts over 40,000 listings and offers everything from illicit goods and substances to hacking tools. With an estimated market value of around $15 million, it has grown into a massive hub for cybercriminal activity. Of course, not all activity on the dark web is criminal, but such marketplaces are where a lot of illegal trade and money laundering happens.
Others sell pirated eBooks, academic materials, and entire premium courses ripped straight from paid platforms. While hiring a hacker might sound like something out of a movie, it’s a very real threat. Businesses may use these services to sabotage their competitors, while individuals may seek revenge or simply want access to private information about someone. Anything from planting malware and stealing sensitive files to hijacking email accounts or breaking into social media profiles. It brings in vendor reviews from other places and verifies them using PGP signatures, so buyers can feel a bit more confident about who they’re dealing with.



