
It advises all users not to trust them, aligning well with the ethos that “ODN” has always advocated. The internet lacks such pure websites, and the dark web lacks just websites. Currently, it seems that both tor.taxi and dark.fail are commendable.
Hoaxes And Unverified Content

Many people go to the dark web to buy things they can’t find elsewhere, but what if what you’re buying is also trying to harm you? Scammers on darknet markets claim to offer legit tools or services, but instead provide you with malicious software that can infect your device. Another great source to find and explore dark web marketplaces or other sections is to visit Reddit’s resourceful forum. You can look for information on /r/deepweb, /r/TOR, or /r/onions, of which the latter is useful to find hidden wikis and more.
Do I Need A VPN To Access The Dark Web Using Tor?
The Tor platform uses an open-source browser that routes data through an encrypted communications stack that resembles the layers of an onion. It relies on a technique called “onion routing” to establish anonymous communication over the public Internet. When the message reaches the final node, it once again appears complete.
Neglecting Basic Security Precautions
Install Tor Browser from the official website, adjust security settings to “Safer” or “Safest,” and only use trusted onion links from verified directories. This blog offers a complete guide on how to access the Dark Web using the Tor Browser, along with step-by-step instructions, security tips, legal warnings, and real-world examples. Following these legal and ethical guidelines ensures responsible use of the dark web, protects your privacy, and helps maintain the integrity and safety of legitimate .onion resources.
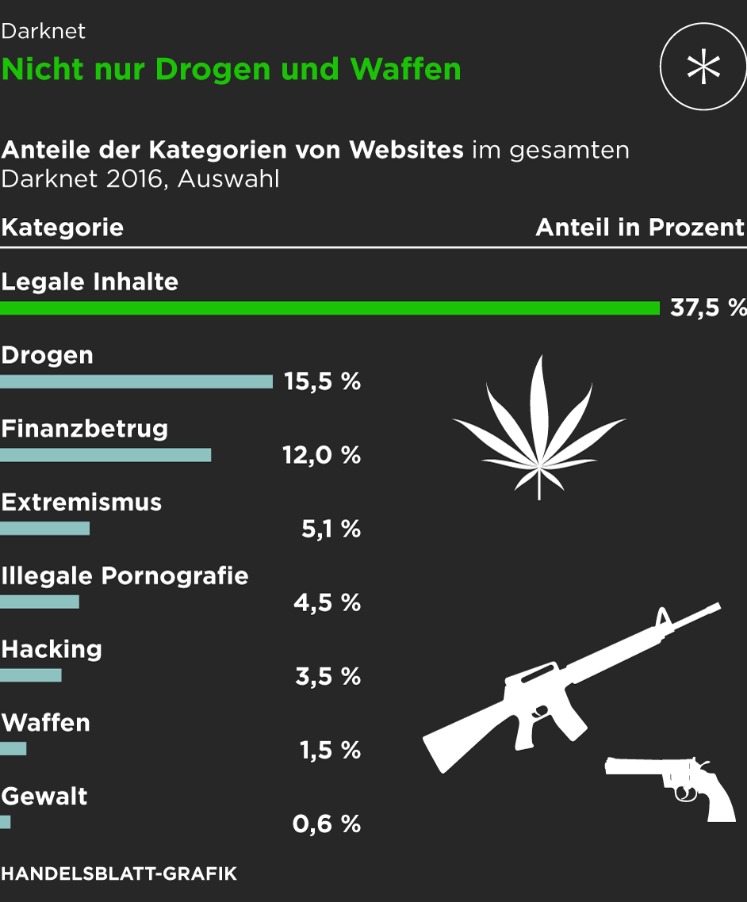
Subscribe To The Blog Newsletter
This is why I strongly advise anyone visiting the dark web to exercise the greatest of caution during their dark online travels. Check out my article for more information about the dark web and how to access it while staying safe. One way to stay safe is to use a VPN while accessing the dark web, so be sure to check out my article on the best VPNs for the dark web. Unfortunately, the dark web is also where underground marketplaces flourish, selling drugs, weapons, stolen IDs and credit cards, and other ill-gotten goods. It is also used to facilitate human trafficking, money laundering, and worse. The dark web is a very popular platform for journalists, political bloggers, and political news publishers, especially for those living in countries where strict censorship shields are the rule.
Why Use Tor For Accessing The Dark Web?
Like most of the markets, STYX supports Bitcoin (BTC), Monero (XMR), and other crypto tokens to keep everyone’s identity hidden on this marketplace. In fact, everything is in English, and the site picks up users everywhere in the world. People visit this market to buy stolen credit cards, personal data, remote desktop account credentials, and logs gathered from information-stealing malware. Torzon Market showed up on the dark web in September 2022, and it’s been growing steadily ever since.
Are Onion Sites Safe?

In 2002 the dark web began to grow significantly when researchers backed by the U.S. The Tor Network provided a way to open safe communication channels for political dissidents, while also offering a channel for American intelligence operatives to communicate from around the globe. Journalists in overly restrictive countries also appreciate the anonymity of the dark web. Silk Road became one of the most famous online black markets on the dark web for illegally selling drugs. The deep web contains sites and pages that are often prevented from being indexed by search engines and contain unlinked content. It can also reside in web archives, non-HTML pages, and so forth.
Search engines on the dark web are a bit of a contradiction because dark web sites by definition are not indexed by traditional search engines. The three nodes separate your IP address from your destination and enable two individuals to communicate without either party, or any middleman, knowing who the other is. Needless to say, it takes your data much longer to travel this way, which means dark web links load slowly compared to indexed sites. Because the IP address of the sender and the recipient are not both in cleartext at any hop along the way, anyone eavesdropping at any point along the communication channel cannot directly identify both ends. Furthermore, to the recipient, it appears that the last Tor node (called the exit node), rather than the sender, is the originator of the communication.
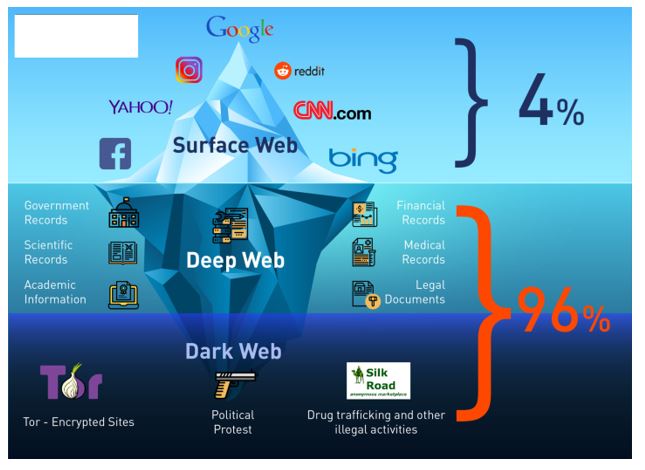
Well-known news websites, such as ProPublica, have launched deep websites. Meanwhile, Facebook also offers dark web access to their social network. The deep web is made up of content that search engines such as Google do not index. Such data includes medical records, financial information, research papers, private forums and networks, and other content. The Deep Web includes all content not indexed by search engines.This isn’t necessarily illegal—it’s just private or restricted.
Best Practices For Accessing The Dark Web
Remember, the Tor browser connects to the internet differently than regular browsers in an attempt to increase your anonymity online. Impreza Hosting is a service that helps you host a site on the Tor network. It provides an .onion URL and an interface for you to manage your Tor site easily. It also boasts that no personal information is required to use the service, and payment can be made with cryptocurrency. Keybase also offers extremely user-friendly secure chat and file-sharing services through its app.
As mentioned before, your ISP and government institutions are not able to see what sites you visit on the Tor network, but they can probably see that you use Tor. Since you’ve now installed the Tor browser, you can safely browse dark web websites and other (previously) hidden websites. From this point onwards, you can enjoy complete anonymity and security while being able to access “.onion” websites and other dark web browser domains. The “Hidden Wiki” (which can be accessed in a normal browser) offers a large collection of dark web links, but be careful, as many of those links are to dangerous websites. Later on, the underlying Tor code was released into the wild under a free license, leading to the formation of the Tor Project. In 2008, the first Tor Browser was released, making it easier for any internet users to access the dark web.
- Unfortunately, the dark web hosts not only explicit but also deeply illegal and disturbing content.
- Since your traffic goes through a series of relays, getting encrypted or decrypted along the way, things slow way down.
- It is similar to an online store, except it’s not the type you’ll find with a quick Google search.
- Search engines do not index these sites and use domains like .onion (for Tor) or .i2p (for I2P).
- It’s still possible to track someone’s traffic pinging through the Tor nodes, though it is difficult.
- For most people and use cases, using only a VPN will offer sufficient privacy with much faster speeds than Tor alone.
By connecting to a VPN before using Tor, you mask your real IP address before it reaches this entry node, adding an extra layer of security and anonymity. Most internet users love a question and answer forum like Reddit or Quora, on the surface web. The dark web version is Hidden Answers, where users can discuss a wide range of topics anonymously. Just bypass your standard web browsers and fire up your tor browser to get on the dark web to access one of the best tor sites. Swiss based ProtonMail is an encrypted email service that is quite popular with the cryptocurrency community.
The goal of an anonymous and privacy network, Tor, is not to engage in the extensive collection of data. However, data is required for understanding, monitoring, and improving the network. Furthermore, data will help to detect attacks against the network and possible censorship events. This service is a good source of statistics if you have a school project requiring research on Tor and the dark web. However, note that the site only uses non-sensitive and public data for the metrics. The BBC news website has a special .onion site, which you need to access via the dark web.
Tor browsers create encrypted entry points and pathways for the user, so dark web activity remains anonymous. The encryption technology routes users’ data through a large number of intermediate servers, which protects the users’ identity and guarantees anonymity. The Onion Internet Protocol address (.onion) also replaces the actual IP address of the sender’s computer, meaning the physical location of the sender is also masked. Only the first and last nodes can reveal the identity of the sender and the content of the message. As conventional browsers cannot display .onion addresses without considerable modifications, Tor clients are also encouraged to use the Tor Browser, a version of Firefox.



