
Each closure reverberates through the darknet community, often leading to the emergence of new platforms—only to face the same fate as their predecessors. The oldest .onion links directory which is actively maintained up to date. Offline payment is a confidence-building factor for those who do not dare or are unable to pay online and those buying higher-value products. Meanwhile, online payment is widely popular and is usually provided by reputable financial institutions, which can have a confidence-boosting role. However, cryptocurrencies are traceable to varying degrees; for example, Bitcoin is easier to trace than Monero (Bahamazava & Nanda, 2022).
Best Tor Sites Available On The Dark Web – Quick List
Moreover, if you must use public Wi-Fi, ensure that you use a VPN to mask your browsing activity and keep yourself secure. Perhaps, the figures can tell you what your personal information is worth when it lands on the dark web. The cost can be exorbitant, but for victims, it’s always higher and devastating. For instance, stolen data can result in unauthorized payments, the draining of accounts, or even registered loans. Moreover, sensitive personal documents are made available on the dark web.
- Check out our list of the best dark web links and how to navigate onion and Tor sites safely.
- Unlike previous isolated arrests, this operation unfolded with a high degree of synchronization — not just across borders, but also between tactical, cyber, and legal departments.
- While some of these markets were shuttered by law enforcement agencies – some took the easy way out with exit scams.
- Unlike regular websites, .onion addresses are long, complex strings of letters and numbers designed for anonymity and can be difficult to remember.
- Proton also offers other security tools besides ProtonMail, such as Proton Drive, Proton Pass, Proton Calendar, and Proton VPN.
- While this is not much compared to standard email services, it is enough for PGP-encrypted messages.
|}
Tor Metrics
Still, they should combine it with other resources to cover a broader range of sites. The ProtonMail Onion site offers the same encrypted email services trusted globally, now accessible anonymously through Tor. This service protects messages from interception and censorship, critical for journalists and activists.
What Is WPA2 (Wireless Protected Access ?
In fact, several businesses can use that service to get rid of competitors, or individuals can use it to gain access to personal information about someone. By keeping these tips in mind and maintaining cautious online behavior, you can safely navigate the depths of the Tor network while ensuring your anonymity. Always stay aware of evolving threats and continue educating yourself about best practices for online privacy. To understand the dark web is to embark upon a journey through its historical milestones.
As such, although a valuable conduit of free speech, the content on Hidden Answers can be distressing, disturbing, and potentially illegal. While it may have a reputation for seedy and dangerous content, many dark web websites are legitimate and useful resources. Keep reading for a rundown of the best dark links you might want to check out. Since the dark web is a hidden and uncontrolled part of the web, there is a high amount of malware infections present there. As a result, you should avoid opening unfiltered sources, torrent sites, and dark web links unnecessarily and downloading every file you come across. Unfortunately, others are fake and fraudulent websites that exploit the reputation of the dark web to con people.
- It doesn’t use JavaScript, which goes a long way toward keeping you anonymous.
- It delivers an uncensored search experience, granting users access to a diverse array of information while effectively excluding illegal content.
- The stolen data can be just anything from full names, credit card details, passwords to social media accounts, bank account information, and social security details, among others.
- The marketplace requires merchants to pay fees to sell their products, helping ensure a certain level of quality control.
- However, cryptocurrencies are traceable to varying degrees; for example, Bitcoin is easier to trace than Monero (Bahamazava & Nanda, 2022).
Some services are genuine; you can get what you want at an agreed fee. Furthermore, it’s critical to understand that Whonix is not a stand-alone browser. It is a component of Whonix, an operating system that functions as a whole inside a virtual computer. It includes all the essential productivity software, including MS Word and an email client. However, there are some significant variances in the background despite the similarities. For example, Whonix’s virtual workstation machine connects to the internal virtual LAN.
Exploring The Shadows: Legal Dark Web Search Engines
STYX market features a robust verification process, making it look more exclusive. In fact, they have a Telegram channel to offer users with live updates. The platform supports Monero (XMR), Bitcoin (BTC), and several others to hide identities. The market has built trust among users as it brings vendor reviews from different places and then verifies them with PGP signatures – that way, the buyers feel confident.

Telegram channels supplement traditional onion sites, blurring lines between the dark web sites and more mainstream communication tools. Despite growing crackdowns from law enforcement agencies, the dark web remains a hotbed of criminal activity, offering everything from drugs to stolen data. Always remember that while the above measures significantly reduce risks, no method guarantees complete security on the dark web. Always exercise extreme caution and verify the legality of any services you access. Watch for unexpected changes in system performance that could indicate malware. Cryptocurrency miners and other malicious software often target dark web users.

Best Dark Web Websites

Sellers often need to pay a deposit to prove they’re serious, and they build their reputation through positive reviews. In 2019, there were approximately 8,400 active sites on the dark web, selling thousands of products and services daily. These sites cater to cybercriminals seeking valuable data, such as credit card numbers, login credentials, and personal information. Today’s cybercriminals spread their activities across multiple platforms, making them harder to track and shut down. Always run the latest version of the Tor Browser to protect against security vulnerabilities.
BBC Tor Mirror

ZeroBin is a wonderful way to share the content you get from dark web resources. It is a reliable messaging tool where you copy/paste a text or image and send it to your addressee. While this is not much compared to standard email services, it is enough for PGP-encrypted messages. The BBC news website has a special .onion site, which you need to access via the dark web. Its goal is to offer anonymous access to the content without being censored, no matter where you live. As a result, it not only focuses on the UK but also provides worldwide news.
Individuals who blow the whistle, known as whistleblowers, play a crucial role in promoting transparency and accountability, often at significant personal risk. They may expose various issues, ranging from corporate fraud to governmental misconduct, in hopes of fostering change and ensuring the public’s right to know. The core functionality of the dark web relies on onion routing, a method that encrypts and routes user communications across multiple servers, known as nodes. Still, the data acquired from this operation will likely fuel years of follow-up actions and targeted arrests. Operation Deep Sentinel reflects a maturing model of cybercrime enforcement.
This is particularly useful for people living in countries with internet censorship, journalists, activists or simply for those who want to protect their privacy. It’s specifically designed for privacy, routing your connection through the Tor network to hide your IP address and encrypt your traffic. Built-in features like script blocking and anti-tracking ensure a safer browsing experience. OnionLand offers a clean design with a simple user interface that includes search suggestions. The search engine allows you to look for old V2 onion addresses, images, and content on I2P.
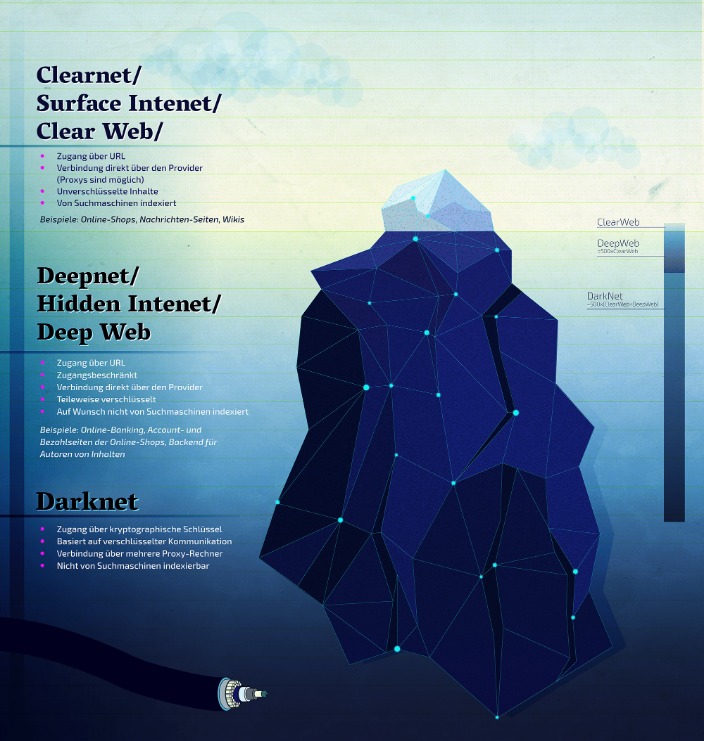
What Are Onion Sites?
Riseup’s services can be accessed on the surface web or via Tor websites if users want to protect their anonymity. The best dark web websites provide access to educational materials, host secure services, or bypass censorship. Dark web websites are hidden under layers of encryption that cloak user activity, which can be a boon to whistleblowers, activists, and others who don’t want anyone tracking their activity. The dark web offers access to unique information and resources you won’t find on the surface web, but staying safe should always come first when choosing a search engine.
The Best Onion Sites On The Dark Web In 2025
With Tor Browser, you are free to access sites your home network may have blocked. For several years, Yahoo was at the apex as the internet’s best web service provider, offering… In today’s digital era, where information is constantly on the move across all digital platforms, an… It is a relatively new provider but offers better features than most established VPNs. The provider also offers a dedicated CyberSec suite that prevents annoying ads and blocks malware and trackers.



