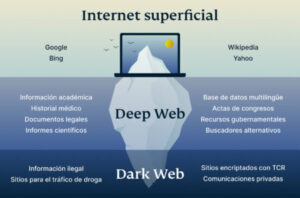
Here you can learn the key differences between Deep Web vs Dark Web vs Shadow Web and...
It’s only accessible through specialized browsers like Tor, which ensures user anonymity and privacy by routing connections...
By following these guidelines, you can minimize the potential risks and protect your online privacy while exploring...
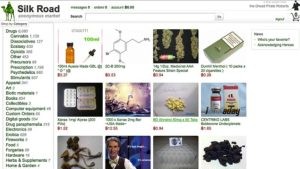
Information in the listings was entered into a spreadsheet for data analysis and statistical calculations. With the...
Certain details of your traffic can be intercepted at the entry and exit points of the node,...
When I told him about my leaked email address, he told me, “Everybody on planet Earth has...
Monitoring for data breaches, using identity theft protection, and implementing multi-factor authentication can reduce the risks if...
First and foremost, never ever use your real info when creating accounts. This means your name, nickname,...
Barratt envisions a future where harm reduction strategies are tailored to the source of the drug. If...
This website offers a convenient way to check if your required website is live at a given...