The internet is a wide landscape that comprises the surface part – the internet that we all know and the hidden portion. The hidden part of the internet is the larger portion that features over 95% of the entire internet. This is the part of the internet known as the dark web, and it’s accessible via mainstream search engines such as Google. Discover everything about what is a darknet market, how it works, security threats related to it, and learn how to protect your data online. Hackers spend a lot of time on the dark web, and it’s not too difficult to get access to hacking tools and data leaks in this part of the internet. However, it’s much harder to get at the people who are doing the uploading and downloading.

Sennheiser GSP 370 Noise Cancelling Gaming Headphone Bluetooth With Microphone – Black

As such, it’s essential to know the risks of dark web access and how to protect yourself from them. We’ve visited and researched the dark web extensively, so below, we’ve outlined the risks we think you should be aware of. In our scenario we are going to legally transfer $1,000 USD out of a regular bank account and into a mathematical system of binary codes, and then enter a neighborhood of the Internet largely used by criminals. This hidden world anyone lets purchase bulk downloads of stolen credit cards, as well as a credit card writer, blank cards, some “on stage” fake identities—and maybe even a grenade launcher they’ve had their eyes on. As cyber threats originating from the Dark Web continue to evolve, businesses—especially small and medium-sized enterprises (SMBs)—must implement proactive security measures to safeguard their sensitive data. A multi-layered cybersecurity strategy incorporating Dark Web monitoring, cybersecurity risk assessments, and employee training can significantly reduce vulnerabilities.
Counterfeit Medicine, Essential Aircraft And Automobile Parts
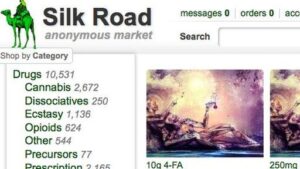
Some are looking for illegal stuff they can’t buy elsewhere, like drugs or counterfeit documents. The story of dark web marketplaces kicks off with Silk Road, launched in 2011. It was the first big site where people could anonymously buy drugs using Bitcoin, and it gained a lot of attention, until it was shut down by the FBI in 2013. Despite growing crackdowns from law enforcement agencies, the dark web remains a hotbed of criminal activity, offering everything from drugs to stolen data. At Cybernod, we specialize in providing cybersecurity services for businesses, designed to protect SMEs from the ever-evolving cyber landscape. Whether you need assistance with dark web monitoring, compliance with data protection regulations, or advice on selecting the best cybersecurity solution for small businesses, our team is here to help.

Criteria For Choosing The Best Dark-Web Marketplaces
Cybersecurity companies and researchers monitoring darknet markets face legal and ethical restrictions. Legally, they are limited to observing publicly accessible areas using tools like the Tor browser, without engaging in unauthorized access or illegal transactions. Markets like AlphaBay and Hansa adopted stronger encryption and expanded offerings to include hacking tools and stolen data. However, these platforms often faced law enforcement takedowns, technical issues, or exit scams, where operators vanished with user funds.
Actually engaging in black market shopping, though, connects you to various kinds of illegal activities. We’ll continue our walkthrough but we are NOT endorsing these activities. This information can help security professionals understand how stolen identities and credit cards are used, how products are fenced or distributed illegally, and more. Drug legalization activists draw parallels between the illegal drug trade and the Prohibition of alcohol in the United States in the 1920s.
- While this topic may seem distant for most people, understanding how these spaces operate is crucial.
- An example of an illegal or black market would be the human trafficking market that engages in the capture of people throughout the world and their sale into various areas, such as forced labor and prostitution.
- Understanding both the lawful and unlawful scenarios helps provide a balanced view of their practical applications in 2025.
- You can legally browse darknet sites for legitimate purposes like research or privacy protection.
Sennheiser HD 450BT Noise Cancelling Headphone Bluetooth With Microphone – Black
Within days, the attackers had exfiltrated sensitive client information, including proprietary marketing plans and billing data. Implementing strong authentication protocols, such as multi-factor authentication (MFA), significantly reduces the risk of unauthorized access. MFA requires users to provide multiple forms of verification, such as a password and a one-time code, making it more difficult for attackers to exploit stolen credentials. SMEs often struggle with limited budgets for cybersecurity, leaving critical vulnerabilities unaddressed. Investing in the best cyber security for small business solutions, such as regular risk assessments, endpoint protection, and dark web monitoring, can provide a strong defense against these threats. Furthermore, conducting a cybersecurity gap analysis ensures that SMEs can identify weaknesses and take targeted action to mitigate risks.
What Makes A Dark Web Market Different From Regular Online Stores?
Besides ever increasing hosting costs, the site will have to contend with authorities, attacks from hackers, and the occasional disgruntled market administrator. Advanced monitoring services like CyberNod offer businesses a critical defense, alerting them to potential leaks and helping protect their assets. By keeping a vigilant eye on dark web activity, CyberNod provides early warnings of compromised data, empowering businesses to take proactive measures to secure their information.
Darknet Websites Uncovered
Escrow services are commonly used to hold funds until transactions are completed, ensuring a level of trust between buyers and sellers despite the illegal nature of their dealings. The dark web, an enigmatic subset of the internet, operates as an encrypted and anonymous network inaccessible through standard web browsers. Unlike the surface web, which is indexed and easily searchable, or the deep web, which houses private databases and unindexed content, the dark web is a haven for covert activities. It facilitates a range of illicit trades, including the sale of stolen data, hacking tools, counterfeit documents, illegal drugs, and firearms. Dark web marketplaces are infamous for being hotbeds of illegal activity, from selling malware and stolen data to offering all sorts of illicit services. Here, we’re going to look at the threats these dark web markets pose, explore recent law enforcement takedowns, and look at the strategies being used to track and tackle these shady activities.
- In most such jurisdictions it is legal to sell the medallions, but the limited supply and resulting high prices of medallions have led to a market in unlicensed carpooling/illegal taxi operation.
- Perhaps, hiring a hacker can feel impossible, but it’s a genuine threat that you need to be aware of.
- DuckDuckGo is a privacy-focused search engine that works as Tor browser’s primary search engine.
- The FBI’s infiltration and dismantlement of Darkmarket, an online virtual transnational criminal organization.
Monitoring dark web markets is crucial, no matter if you are a business or individual, as you can then proactively identify and mitigate potential breaches and cyber threats. The dark web hosts a wide range of sites — from whistleblower tools and secure email platforms to underground forums, black markets, and dark web mirrors of legitimate news outlets. Torch is one of the more established dark web search engines, designed to help users navigate the Tor network and discover onion sites. Unlike traditional search engines like Google or DuckDuckGo, Torch indexes hidden websites that operate beyond the reach of the surface web. But users should always be cautious and avoid clicking unfamiliar or untrusted links to steer clear of scams or malware. You can use dark web monitoring tools, such as NordVPN’s Dark Web Monitor, to check if your data has been leaked.
The dark web or darknet is a computer network that uses encryption and randomized relay systems to mask a user’s identity, IP address, and browsing history. Tor Browser, built on Firefox, encrypts your traffic across 3+ relay nodes, enabling access to .onion sites. In 2025, it powers 2.5M+ daily users, with Germany leading in usage (followed by the U.S.). Along with the aforementioned factors, international cooperation is key to success in these operations. For example, the takedown of Monopoly Market was coordinated by Europol and involved authorities from nine different countries. The operation, codenamed SpecTor, led to the arrest of 288 vendors and highlighted the importance of shared intelligence and collaborative efforts across borders.

Also a contributor on Tripwire.com, Infosecurity Magazine, Security Boulevard, DevOps.com, and CPO Magazine. To remain anonymous about your purchases on the dark web, always use cryptocurrency as your mode of payment. If a seller encourages you to opt for other well-known and commonly used payment methods, then the person is likely to be a scammer, and you must not make any deal with them.
These features help establish trust between buyers and sellers, providing users with a sense of security that many other markets lack. As cyber threats grow more sophisticated, organizations are keeping a close watch on the dark web. Companies use dark web monitoring to scan for leaked data, stolen credentials and breach indicators, helping them track and identify perpetrators. But let’s be realistic, the best defence isn’t just playing detective after the fact. It’s making sure your sensitive information never lands there in the first place.
Unlike Bitcoin, which records every payment on a public ledger, Monero conceals all transaction details by default which makes them nearly impossible to trace. Accessing the black market can be a daunting task, especially for those who are unfamiliar with its inner workings. However, with the right knowledge and precautions, it is possible to navigate this underground economy safely and efficiently.
Why Is It Critical To Monitor Dark Web Marketplaces?
What current policing strategies neglect is that dark web markets are not isolated to the storefronts that are the popular target of crackdowns. These are communities stretched across dark and surface web forums which develop shared tutorials and help one another adapt to any new changes. These closures bind users together and foster a shared resilience and collective experience in navigating these environments. This shift will likely drive forum operators to introduce features like automated escrow services and enhanced anonymity to attract users. Buying illegal substances, stolen merchandise, and counterfeit currency or goods online poses significant risks for both the buyer and the seller. As the DNM builds a small pool of users and sellers, it will snowball into a lucrative operation IF the service remains reliable and secure.