For instance, dark web websites could be infected with malware, or designed as scams to gather stolen data. Tools such as VPNs can make it somewhat safer to browse, but people should still exercise extreme caution whenever visiting web pages on the darknet. By exploring these categories of resources, users can discover that the dark web’s landscape is more nuanced than popular portrayals suggest. Education, activism, journalism, and creativity all find refuge here, protected by layers of anonymity.
How Did We Select These Best onion Sites?
TOR is a network of servers that allows its users to browse the internet anonymously. It’s a nonprofit agency whose main purpose is to develop and research online privacy tools. Believe it or not, getting on the dark web is pretty easy, you just have to know which tools to use.
Just as you explore hidden corners of the internet, you need to secure your data on the go. Easily initiate data encryption on your external drives and disks, ensuring compliance with your specific company policies. Encryption-2-Go offers controlled encryption, container-based or directory encryption, and even detects existing BitLocker To Go encrypted drives. With configurable user selection dialogs, it provides a user-friendly experience while maintaining strict security.
Avoid Sharing Personal Information
- One of its best features is Anonymous View, which is a free proxy that masks your identity while you’re browsing sites.
- PasterNinja is the Darknet Pastebin, or in other words one of the many legal Tor links alike Pastebin on the Tor network.
- So, whether you seek refuge from oppressive regimes, are searching for answers to hard or embarrassing questions, or are trying to share confidential information securely, there is something for you.
- That’s why many people choose to do so anonymously on the dark web, rather than using the clear web version of the site.
- In addition, you can connect your Keybase account with X, GitHub, or Reddit to let people easily trust that they are talking to the actual person.
The Darknet is a subset of the Internet operating over encrypted, anonymous overlay networks that require special software like Tor, Freenet, or I2P. Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing. Dark web surveillance involves monitoring information on the darknet, such as to identify compromised credentials being sold, or to track forums to anticipate (and prevent) cyberattacks. With cryptocurrency prices fluctuating, crypto-laundering gangs can capitalize on market volatility to conceal illicit funds, and use botnets to illegally mine cryptocurrency data. While no single tactic is foolproof, a layered approach—combining technical, operational, and psychological defenses—greatly improves your safety and confidence when navigating the dark web. While no approach is foolproof, a thoughtful, criteria-driven strategy ensures a more secure and beneficial experience on the dark web.
Risks That Dark Web Search Engines Pose
Besides, victims of crime may want to hide their identities from their perpetrators. Nonetheless, if whatever you do is deemed illegal in your country, you can get into trouble. Nowadays, many people use the Tor browser to surf the public internet and navigate the deeper parts anonymously. Therefore, the legality of the dark web will mainly depend on how you use it.
AzureStrike – Offensive Toolkit For Attacking Azure Active Directory Environments
It uses TrustedServer technology on the entire server network to wipe out your data after every session. The Tor browser allows you to browse the internet anonymously and visit inaccessible sites. Your online activity and communications remain private and secret on the dark web.
- Tor, or “The Onion Router” is by far the largest of these darknets.
- Facebook is aware of attempts by many governments to restrict access to a tool that allows strangers across the web to talk and collaborate freely.
- Besides monitoring and improving the network, the data can be used to detect possible censorship or attacks.
- Even the best privacy tools are only effective when patched against the latest threats.
One of the most common threats in 2025 comes from fraudulent marketplaces. These sites are crafted to look like real, trusted markets, complete with product listings, vendor ratings, and support pages. But once you send cryptocurrency to fund your account or make a purchase, the funds vanish — and so does the site. Accessing dark web sites isn’t hard, but doing it safely requires the right tools and awareness of common threats.
Types Of Dark Web Sites (and What Really Goes On There)
The dark web and the deep web are often used interchangeably, but they’re two distinct concepts. Onion sites (aka Tor sites) are websites only accessible on the dark web; you can’t view them using a regular browser. Their URLs (aka dark web links) have .onion as the domain, instead of the common surface web domains like .com or .net.
Each search engine opens the door to potentially harmful content, making caution a necessity. Since it’s an old search engine that hasn’t changed much, its indexing, while broad, is not always reliable. Many links found there are outdated or broken, and it provides very little metadata or context for search results. Torch also offers no real filtering or sorting options, making it inefficient for users who need to conduct targeted searches. This website used to host over 7,000 onion sites, giving users access to many dark web links. The listed links were well-grouped for a simpler browsing experience.

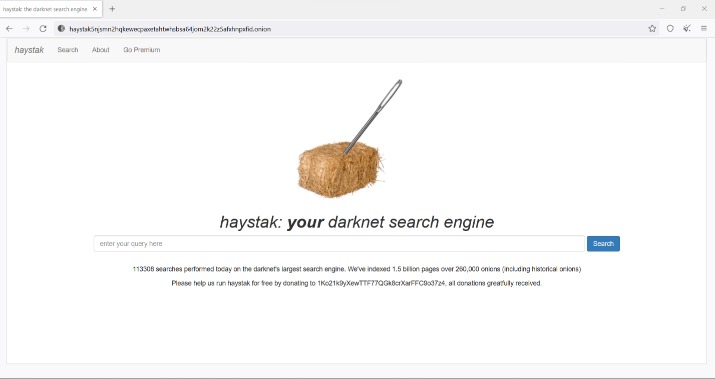
ZeroBin offers an extra secure version of this service by only encrypting and decrypting text in the browser, meaning their servers have no knowledge of what is passing through it. One of the most popular ways to get around the dark web is not to use a search engine at all. Just like in the old days of the internet, the dark web maintains numerous indexes of sites, like The Hidden Wiki. Haystak also offers a premium version that allows advanced search, access to historical content, and email alerts. When you try to connect to a .onion website, Tor will route your traffic through three or more randomly chosen nodes before it reaches your destination website. Each server adds a layer of encryption, and this layered system is what lends The Onion Router its name.
The Top 7 Dark Web Marketplaces In 2025
Just don’t be stupid and ruin your lovely life by doing foolish things. It isn’t that difficult to do, but it’s sometimes it can seem tedious to take extra precautions. Just maintain strict security measures and then go to the dark web; that’s all there is to it.
Protecting Against Malware And Exploits

As a result, we want you to stay safe and anonymous by using a paid VPN service whenever you surf this dark web platform. ProPublica is a prominent investigative journalism platform on the regular and dark web. This duality allows users to choose whether to access the platform openly or anonymously. The advantage of this version is that you can effectively create a Facebook account anonymously or use this social media platform in a restricted region. Consequently, you’ll have maximum privacy while sharing opinions and anti-oppression resources. However, there’s no guarantee that all the links on this site are working.
Access The Dark Web Index
The hidden wiki is an encyclopedia like Wikipedia, which is in the deep web, is one of the most complete guides to access the pages with onion links. That is why in 2006 they created “the most private search engine in the world”, which does not record, track, or share your personal data. Over the years, they added many additional privacy features, such as “Anonymous View” for added protection. They are located in Europe, where privacy laws are among the strictest in the world.
The use of the dark web raises suspicion as it shows there is something you want to do privately. Remember that illegal activities can still incriminate you, whether you are using a Tor browser. For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved.
It’s a go-to for users who want structure and security in their dark web exploration. These sites often appear in onion directories, but they come with extreme risks. Many are scams designed to steal money, while others are honeypots monitored by law enforcement. While you don’t need to log in to access any of the dark web links listed here, you can’t find them with a search engine like Google. The only way to access the dark web is by using the correct browser and knowing the URLs of the pages you want to visit.



