Major active platforms include Abacus, Russian Market, BriansClub, and Exodus. Law enforcement takedowns, such as Archetyp, demonstrate both impact and adversary adaptation. For cybersecurity professionals, focusing on payment methods, vendor migration, and marketplace specialisation offers the most effective path to actionable intelligence. Monitoring active marketplaces offers early access to malware kits, credential dumps, and fraud tools. Tracking vendor migration—such as from Archetyp to Exodus—provides insight into tactical shifts. Focusing intelligence collection on specialised marketplaces yields better ROI for threat detection and proactive defence.
- The structural change in the multiseller network and the resilience of the multibuyer network.
- Law enforcement agencies continuously improve their ability to trace transactions and monitor marketplace activity.
- While there are several darknet markets, each features unique characteristics tailored to various user needs.
- Law enforcement darknet operations require highly trained and specialised officers.
- The cost can be exorbitant, but for victims, it’s always higher and devastating.
- Silk Road transactions were made with Bitcoin, so it was necessary to exchange cash into Silk Road Bitcoin before purchasing anything — like exchanging cash for tokens at an arcade.
Payment Methods Overview
Administrators and sellers on dark web marketplaces had a better 2023 than the previous year, pulling in an estimated $1.7bn in cryptocurrency-based revenues, according to new Chainalysis data. Archetyp Market delivers 28,000+ listings and $3.5 million in monthly trades using BTC and XMR, securing a 6% market share. With 12,000+ users and 900+ vendors, it boasts a 95% vendor rating—ideal for quality-focused dark pool trading.
FAQs About Dark Web Marketplace Links

Transactions within dark markets predominantly involve cryptocurrencies like Bitcoin, Monero, or Ethereum. These digital currencies provide a degree of anonymity, as transactions are recorded on a public ledger but do not directly link users to their real-world identities. To purchase illicit goods or services, users deposit cryptocurrency into an escrow system or directly to the seller, and the cryptocurrency is held until the buyer confirms the satisfaction of the transaction. In contrast to the other types of sellers, the median income of U2U-only sellers increases after operation Bayonet. Moreover, we observe a trend of increase in their median income relative to the value before operation Bayonet—an increase of almost six times by the end of the period of observation (see Supplementary Information S4). Further supporting this interpretation, we observe that the trading volume of the U2U network increases after Bayonet, while the trading volume of markets decreases (see Supplementary Information Section S4).
Surge In New Scams As Pig Butchering Dominates
Therefore, the S2S network can be seen as a proxy for a distribution network of illegal products. The darknet markets are a hotbed for selling stolen personal information. The stolen data can be just anything from full names, credit card details, passwords to social media accounts, bank account information, and social security details, among others.
This guide outlines different ways of safely accessing dark web stores and the list of reliable dark web marketplaces you can consider visiting in 2025 for research and monitoring purposes. Given the explosive growth of these markets, organizations must prioritize proactive threat monitoring. Axis Intelligence provides dark web surveillance solutions that help businesses identify leaked credentials, fraud attempts, and malware risks before they escalate. Known for its publicity stunt releasing millions of stolen card details for free, BidenCash specializes in credit card fraud and identity theft. While China-based vendors are frequently referenced as the source of precursors for dangerous synthetic drugs, their involvement in machinery sales is also an important aspect of the drug supply chain.
- In particular, we analyse networks of ‘multihomers’, defined as users that are simultaneously trading in multiple markets.
- But somewhere between production and purchasing, things can get dirty.
- It offers a wide range of goods and services with robust anti-DDoS protection (with military-grade security protocols) and no JavaScript, ensuring privacy and uptime.
- For instance, whistleblowers, journalists, and activists may use the dark web to communicate securely and anonymously.
Essential Security Tips For Using Dark-Web Marketplaces
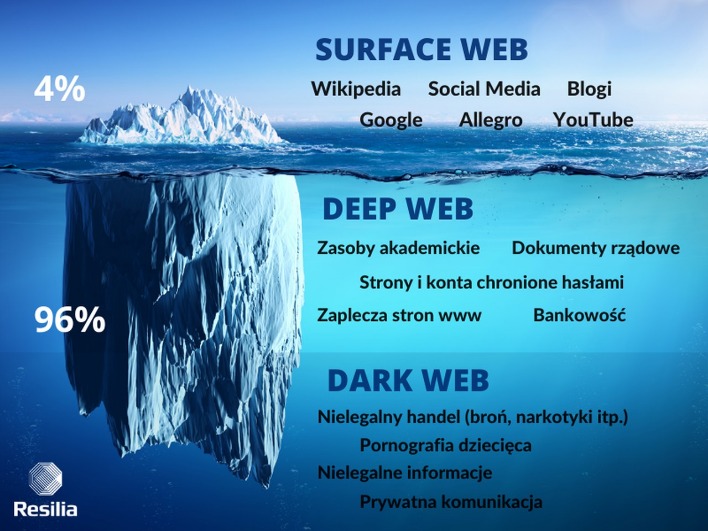
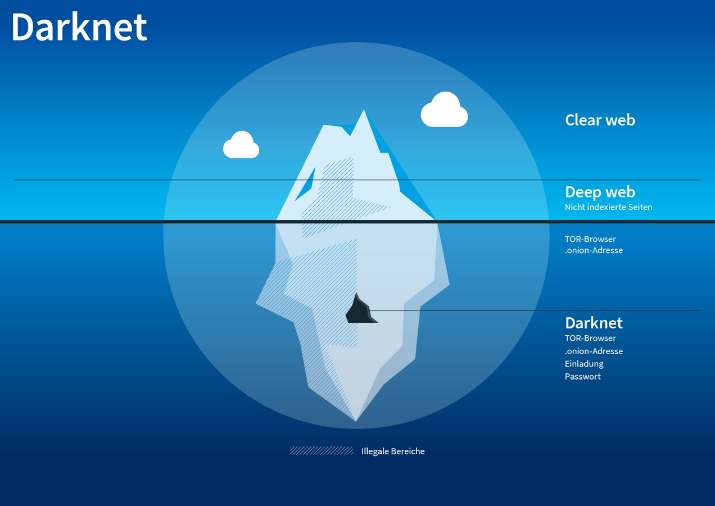
This area comprises websites and content that are purposely kept hidden from public view. Criminals seek to remain anonymous by hiding their operations and identity using technical methods such as encryption, and non-technical means such as communicating in English instead of their native tongue. Based on their communication alone, it is challenging to identify the whereabouts of specific perpetrators as many of the largest Darkweb marketplaces offer services and products worldwide. If you’re using a browser like Tor and visiting .onion websites that aren’t accessible through regular search engines or browsers, you’re likely on the dark web. These sites often look basic or outdated, and their URLs are lengthy strings of random letters and numbers.
We use data of DWM transactions on the Bitcoin blockchain pre-processed by Chainalysis Inc. Although other coins are used, such as Monero recently, Bitcoin is still the mostly used in the ecosystem, being supported by more than 93% of markets7,9. The pre-processing relies on established state-of-the-art heuristics to cluster addresses into entities, such as cospending, intelligence-base, and behavioral clustering39,40,41,42. The resulting data set includes for each transaction the source and destination entities, the time, and the value of the transaction.
Anonymity Through Tor
During our tests for the research, we were able to register with a bogus email and a random username. All that one can expect from a deep web marketplace when it comes to anonymity and security. With these stolen credentials, the suspects purchased ghost gun parts and tools from a variety of legitimate websites, which they used to build ghost guns with a 3D printer, and sell for cash. A Manhattan district attorney successfully used this evidence to bring charges against one of the suspects. Deposits span from the hundreds to the tens of thousands of dollars, and the average deposit amount in 2024 was over $2,000. China-based Abacus vendors have many listings for research chemicals.
Crypto-native Money Laundering
All the payments were made through cryptocurrency, further enhancing marketplace anonymity. The users on this site can review and rate the products that promote reliable and fraudster vendors. In 2023, the New York Police Department (NYPD) Intelligence Bureau, which predominantly handles counter terrorism cases, received a tip about two people in New York City involved in manufacturing and selling ghost guns. Using a series of search warrants and subpoenas, the NYPD found the suspects’ online raw material purchases, and uncovered a crypto dimension to the case, not publicly shared until now.
DNMs are inherently dangerous places and its users risk losing their money, their freedom, and their lives.Are you suffering from drug addiction? Tor2door’s a standout since 2020 with 20,000+ listings and a custom design that’s not off-the-shelf junk. BTC and Monero accepted, with multi-signature escrow and global shipping—vendors love it, and I’ve seen why after snagging some rare stuff hassle-free. Drugs dominate, but digital goods are picking up—ties into the Telegram trend with side hustles. They’re talking AI search tools for 2025, which sounds slick—finding stuff could get way faster. DrugHub popped up in 2023 and quickly hit 15,000 listings—all drug-related.
What Are Onion Sites?
As mentioned earlier, it’s difficult to track non-crypto-native crime cases at scale without context — often only known by law enforcement, financial institutions, crypto services and/or victims. Nonetheless, some of our customers have provided us with information for address attributions, allowing us to better understand the state of non-crypto-native money laundering in Japan. We published a blog last year addressing our on-chain analysis on a Japan-based money laundering case that started with non-crypto native crimes. Vendors on Hydra also offered services such as “Hacking for Hire,” “Ransomware as a Service” (“RaaS”), and a myriad of money laundering features. Though the drug transactions were limited to Russia and its geographic neighbors, the cyber and money laundering tools were available to anyone in the world willing to pay. Conversely, transaction networks obtained from the blockchain contain the entire transaction data of the DWMs and U2U transactions, allowing a thorough investigation of the ecosystem as a whole.
In light of this, we have chosen the parameters conservatively, obtaining estimates for the number of sellers that are in general smaller than the ones produced by other methods. Second, our approach does not explicitly classify buyers, which are entities that were not classified as sellers. There is a gray zone in which some sellers and buyers may not be easily distinguishable in transaction networks. For instance, there may be sellers that make a small amount of transactions, or spend more than receive, which we would classify as buyers. Despite consistent results, this clearly leaves space for refinements. Future work may further extend the approach presented here, for example using machine learning methods to capture further behavioral regularities.
Often portrayed as the internet’s shadowy underbelly, the Dark Web hosts marketplaces offering everything from privacy tools and digital currencies to more questionable, or outright illegal, products and services. Dark web markets have exploded in scale and reach in 2025, becoming the most dangerous hubs for trading drugs, stolen data, and hacking tools. These anonymous marketplaces—operating mainly on the Tor network—are now a primary threat vector for businesses and cybersecurity professionals.