Business operational data, such as operational data, financial data, intellectual property, and trade secrets can be found on the dark web. As you are now familiar with the three different sections within the entire world wide web, let’s take a closer look at how you can access the dark web anonymously. Especially for these people, the dark web is the perfect platform to communicate and publish information without having to worry about imprisonment or any other form of retribution. Those who access the dark web do so via the Tor (The Onion Router) browser. The release of Freenet in 2000 is considered by many as the start or founding of the dark web. University of Edinburgh student Ian Clarke created Freenet as a thesis project.
What Is The Dark Web And How To Access It?
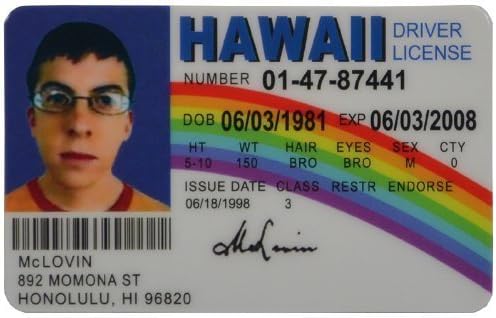
Alternatively, you can send an email to the address on the footer of each page. Their id used all latest technologies that state id have including magnetic strip barcodes, inviable UV ink, precise edges, etc. that pass almost every fake id scanner. Fraudsters would spend hours meticulously crafting each detail to fool security checks. But today, AI has turned this once-difficult task into something shockingly easy.
ID Scanner Accessories Tab
Many dark websites are perfectly legal and safe to use and, in many cases, are better for your privacy than clear websites. For a number of technical reasons, it’s much faster and more reliable than Tor. The peer-to-peer routing structure is more advanced, and it does not rely on a trusted directory to get route information. I2P uses one-way tunnels, so an eavesdropper can only capture outbound or inbound traffic, not both. A VPN allows a user to encrypt all internet traffic traveling to and from his or her device and route it through a server in a location of that user’s choosing. A VPN, in combination with Tor, further enhances the user’s security and anonymity.
Telegram carding groups have become a significant threat in the cybercriminal community, with tens of thousands of members easily accessible through the chat application. Such type of data is likely to have been compromised online, making it a red flag for would-be fraudsters. Group-IB’s cybercrime research unit has detected two major leaks of cards relating to Indian banks in the past several months. To avoid falling victim to these scams, it’s essential to be cautious when entering sensitive information online. This includes using strong passwords and enabling two-factor authentication.
Awazon became the successor of the popular AlphaBay market, which the authorities shut down successfully in July 2023. Like any other site of such nature, Awazon Market isn’t free from risks, so be careful while accessing it. If you choose to visit the dark web, you must take the necessary measures to protect your privacy and security.
Criminal Exploitation
Plus, it lets you set your location for local results, manage safe search filtering, and there’s even an AI “Assist” tool that provides AI search results — so you don’t have to visit web pages to find your answer. These checkers are often offered and sold on the dark web, and are complimentary tools that individuals and organizations use to verify credit card information. Card checkers are tools used by threat actors to verify the validity and authenticity of credit card information they purchase on the dark web. The use of JavaScript-sniffers, also known as Magecart, has led to a significant increase in stolen payment card data. Regularly monitoring your credit card statements can help you detect any suspicious activity, such as unauthorized transactions.
Types Of Fake IDs: A Closer Look
Offers complex ID features, including raised text and scannable barcodes. Offers a long history of operation, with a reputation for delivering high-quality products. Biometric technology is leading the charge in next-generation verification.
Why Traditional Document And ID Verification Methods Fail
The use of the dark web raises suspicion as it shows there is something you want to do privately. Therefore, the legality of the dark web will mainly depend on how you use it. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom.
Wizardshop.cc was established in 2022, and offers a wide range of leaked CVVs, database dumps and even RDPs. In the past 6 months, the site has increased the volume of cards sold, placing itself as one of the top sites selling credit cards today. The site has a unique news section, where the admin updates the buyers about new leaks and dumps, the source of the dumps, structural site updates and more. Another unique feature Brian’s Club has is the auctions it offers during which users can reserve, bid, and outbid other users who want to purchase exotic BINs. Active buyers are also eligible for free gifts and dumps depending on their volume.
Trusted Directories
This is the best place to get short and reliable links to an unalterable record of any webpage across government and corporate websites. Unfortunately, it requires you to have an invitation code to create an account. This means you have to know someone who is already using the platform. Even without the code, you can visit the security section to get tips on improving your daily life privacy. The goal of an anonymous and privacy network, Tor, is not to engage in the extensive collection of data. However, data is required for understanding, monitoring, and improving the network.

Maintain Account And Password Cleanliness
If you’re in a coffee shop or anywhere else you don’t trust network security, use a virtual private network (VPN) to encrypt all communications. But if an attacker has access to an unencrypted network that you’re using, it’s easy to view your account data and steal or alter your information. Check out my guide to the best VPNs if you are interested in picking one.
- Manual ID verification depends heavily on human judgment, which can be inconsistent and easy to manipulate.
- Finally, many people consider the dark web a necessary tool for privacy and freedom of speech.
- Deep and dark web credit card sites include forums and marketplaces that host the trade and share of illicit content relating to credit cards.
- Otherwise, there’s a good chance of falling victim to a phishing scam like this fake Bitcoin mixer.
- University of Edinburgh student Ian Clarke created Freenet as a thesis project.
- Here are some methods to thwart unauthorized access to your data repositories.
Stay Safe On Dark Web Websites

This means the VPN provider doesn’t see your real IP address and the VPN protects you from those bad exit nodes. So, if you want to know how to access the dark web safely, you need to understand that the vast majority of the dark web, or dark net, is only accessible through the Tor browser. It’s like an iceberg – The visible tip above water, known as the “surface web” represents the familiar, searchable content. But lurking beneath lies the expansive, mysterious “deep web” or“dark net” – the gigantic submerged part that remains invisible to standard searches.

Authorities seized extensive data, cryptocurrency wallets, and arrested several key administrators and high-profile vendors. Property managers need a solution that includes a biometric liveness check. This step requires the applicant to take a live photo of themselves and then upload their issued ID, ensuring that the ID matches the photo taken in real-time. This added layer of security can save property managers from costly lawsuits and potential damage to their reputation.
Case Studies In Lawful Identity Reconstruction, Lessons For Safe And Compliant Transitions
Monitoring dark web forums is an important source for analyzing current cyber threats. Today, although threat actors broadcast their illegal activities via applications such as telegram, dark web forums are still one of the current content sources. According to the analyses made by ThreatMon analysts, there are important findings detected and obtained from dark web forums as the first source. With the detection of exploits, zero days, malware, etc. content obtained from dark web forums, proactive intelligence is developed by analyzing current malware.