Fraudsters who have hacked into systems and stolen data oftentimes turn to the Dark Web to sell what they’ve gathered. Common items for sale include credit card data, credentials, and even fingerprints. The price tag for these items may be surprising, with usernames and passwords selling anywhere from $.10 to $1 and fingerprints selling for about $2 each. You can also find websites to download copyrighted material such as music, movies, games, software, and even Netflix credentials.
Media Outlets With A Secret Door
The sharing of illegal pornography and discussion of illegal sex acts account for a significant portion of dark web traffic. The extent of the problem became clear in 2015, when the FBI shut down a dark web site on Tor named Playpen that hosted 23,000 sexually explicit images of minors. These marketplaces use .onion domains and are accessible only through the Tor browser. Famous examples of Dark Web marketplaces include now-defunct Silk Road and AlphaBay. Transactions on these illicit marketplaces are made using cryptocurrencies to maintain user anonymity.
- The dark web is the smallest and least accessible subsection of the hidden web.
- A discrete online identity, which has nothing to do with your present one.
- Supreme Court will allow the FBI to search and seize any computer that’s using the Tor browser or VPN.
- This connection methodology enables users to interact with the dark web with minimal risk of their activity being tracked or otherwise exposed.
- The dark web refers to any number of self-contained, encrypted overlay networks that live on top of the internet, inaccessible save for special tools and protocols, hence dark.
This anonymity is not necessarily used exclusively for illegal activity. For instance, political dissidents under an oppressive government might use the dark web for communication. However, the deep web can also host illegal content such as pirated media. Anyone can access this material without needing a different web browser such as Tor. Many websites on the deep web avoid showing up in search engine results by blocking the bots that ‘crawl’ the internet to collect information for search engine indexes.
Exposure To Harmful And Illegal Activities
Remember, whether you’re diving into the depths of the deep web or cautiously exploring the dark web, always prioritize your security and ethical considerations. Discover what is the deep web vs dark web and learn their key differences, use cases, and how to navigate them safely. Even clicking a single link could result in legal scrutiny or malware infiltration. There’s also an increased chance of downloading malware, leaking credentials due to a phishing scam, or falling victim to financial fraud due to the lack of oversight. Accessing the Deep Web generally involves fewer risks compared to the Dark Web, but there are still some considerations. It’s important to note that the Dark Web is not inherently illegal.
New Bitsight TRACE Security Research
Overall, Subgraph OS is a secure and privacy-focused operating system well-suited for high-risk environments. Additionally, you can opt for Subgraph OS as a second option to Tor. As listed above in our article, even respected organizations like the BBC and ProPublica have a version of their site on the dark web. Some markets even sell privacy tools, but you are more likely to run across counterfeit prescription pills and stolen identities.
Is It Illegal To Visit And Use Dark Websites?
First, you need a web browser that’s capable of utilizing the Tor protocol. In theory this should make your deep web browsing (as well as your regular web browsing) entirely private from interlopers. However, since your traffic is routed through nodes that you don’t have any control over, you are at the mercy of whoever operates these nodes. If you use the widest definition of the deep web, then it’s a vast ocean of websites. If you’ve followed the news in the last two decades, you’ve probably heard stories and seen headlines about the deep web or dark web. However, you might have found yourself asking, What is the deep web?
How To Access The Deep Web Using Tor
It’s only when the packet reaches the final destination that the last layer of encryption is removed and the intended recipient gets the original data. After all, some websites on the deep web are like those on the open internet, except that they are hidden behind a paywall or protected via passwords to limit access. On the other hand, the dark web’s main application is to provide anonymity to website owners and users. The obscurity makes the dark web the perfect platform to host websites for illegal and illicit activity.
Legal Implications

The internet’s deeper layers—namely, the deep web and dark web—represent distinctly different realms of online interaction. Understanding the fundamental differences between the two is crucial for safe navigation in today’s digital world. Prior to Keeper, Darren served as an advisor to JiWire, now called NinthDecimal.

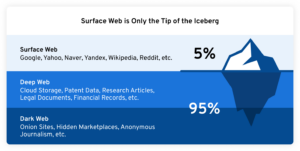
The deep web vs dark web are often misconstrued as being one thing when in reality they represent two different levels of the internet. The deep web refers to all that is accessible on the internet that is not indexed with those typical search engines. This would include a very broad range of content such as private databases, academic resources, and password-protected sites. Unlike the surface web, which is easily accessible and often serves legitimate purposes, the deep web holds valuable information that typically requires specific access credentials or subscriptions.
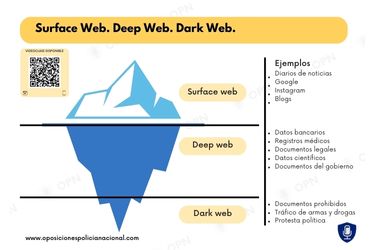
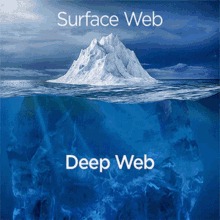
Using our ocean and iceberg visual, the dark web would be the bottom tip of the submerged iceberg. It is also advisable for users to look for phishing scams, where criminals share communications that seemingly originate from a reputable source. Unwitting users then share sensitive personal information by falsely believing that these communications are legitimate.
Though no one should bat an eye just because you’re attempting to access the dark web, keep in mind that in some countries, like the United States, even a simple foray can get you in trouble. These groups develop their own sophisticated malware, sometimes combined with pre-existing tools, and distribute them through “affiliates”. Medical records, fee-based content, membership websites, and confidential corporate web pages are just a few examples of what makes up the deep web.
- It focuses on privacy, censorship resistance, and ensuring free access to content.
- This part of the web contains everything from password-protected sites and data not accessible via public web pages to private intranets, academic content, and more.
- The security implications of the surface web differ significantly from its hidden counterparts.
- Each layer of the internet requires users to approach their activities with mindfulness, adopting necessary precautions to protect themselves against potential threats.
- The dark web news site Deep.Dot.Web teems with stories of buyers who have been arrested or jailed for attempted purchases.
The Multiple layers of encryption resemble the structure of an onion. If you think that search engines like Google (there are more!) know about everything on the internet, you’d be wrong. Some stats from from Worldwidewebsize.com show at the start of November 2017, search engines have indexed at around 4.57 billion pages .
The dark web was designed mainly to provide users with more privacy. The simplest definition for the deep web I can come up with is “It is any and all content which is unindexed, and can’t be found via traditional search engines like Google, Yahoo, Bing etc”. This has non-indexed content and cannot be accessed with a regular Google search. There are broadly two categories of deepweb – one is obscurity or anonymity, while the other is authenticated. There are several tools used for reaching these parts of the internet. The TOR (The Onion Router) maintains the most popular tool for Dark Web access.



