
Following these precautions will help you explore the Hidden Wiki and the dark web with greater safety and confidence. Cryptocurrency tools help maintain privacy and trust during financial transactions on the dark web. The Wasabi Wallet is a Bitcoin wallet that uses CoinJoin mixing to obfuscate transaction trails, enhancing user anonymity. BitBlender provides a mixing service that pools multiple users’ coins to anonymize their origins and destinations.
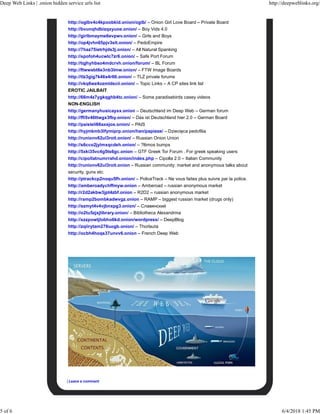
How To Access The Deep Web?
Altenen is probably the legend when it comes to the world of online fraud – it has been around for a long time. The forum focuses mainly on credit card fraud, but it also covers other topics such as hacking, cracking, and several other aspects of cyber scams and IT. Like BFH and some other forums listed in this article, Cracked also operates right on the surface web, then you don’t have to look any further.

Why Can’t I Access Onion Sites?
A robust antivirus can help block malware and other online threats, even on the dark web. Sites stored in the index are then ranked based on a variety of different factors, which is what decides how far up on the results page the sites appear in a search. For several years, Yahoo was at the apex as the internet’s best web service provider, offering…
Image Hosting — Upload & Share Images
Based on our observations from analysis on dark web data using Lunar, we’ve identified the top 7 marketplaces on the dark web in 2025. We developed Lunar to monitor the deep and dark web, including dark web marketplace sites. Darknet markets, their wares and services, hacking, carding, fraud, CP, and otherwise involuntary/illegal pornography are off-topic and unwelcome here. Apart from the dark web markets that are operating online today, some raided platforms influenced many markets. Some fake sellers take your crypto and never ship what you ordered, or phishing sites that look like real marketplaces but steal your login info.
Ahmia primarily indexes .onion sites on the dark web, not both surface and dark web content. It is specifically designed to make hidden services on the Tor network more accessible. It offers a clean, user-friendly interface that simplifies the process of searching for hidden services. So, conducting dark web social hubs’ monitoring can offer significant intelligence for cybersecurity professionals and law enforcement. That way, they can easily combat criminal and illicit activities and also help to stop data breaches and several other potential malicious attacks.
Dark Web News And Media
- It blocks browser trackers and resists fingerprinting, which helps maintain your anonymity while browsing.
- Telegram channels supplement traditional onion sites, blurring lines between the dark web sites and more mainstream communication tools.
- Many exit nodes are actually operated by law enforcement and scammers.
- For example, one of the most common ways to access both the deep web and the dark web is through Tor.
Cyble’s platforms, such as Cyble Vision, monitor the dark web for emerging threats, providing real-time insights to protect organizations from cybercrime. By leveraging such tools, businesses and governments can protect their data and communities from cyber actors. Launched in 2013, XSS is one of the longest-running forums in the dark web. Initially known as DaMaGeLaB, the forum rebranded in 2018 after the arrest of one of its administrators. XSS is primarily focused on hacking, corporate access, and data leaks, making it a hub for cybercriminals and hackers.
Most internet users want to use the dark web safely, but it’s still important to be careful when using any onion browser. Apart from the best onion sites listed here, you must be careful with the Tor pages you visit. Search engines and corporate websites might be OK, but even a popular Tor website like Hidden Wiki can show illegal deep web links that jeopardize your online safety. Unlike traditional search engines, it doesn’t track or store personal information, ensuring your searches stay private.
Is It Illegal To Access The Dark Web?
- Therefore, the organization should gather all the necessary info to guide them in identifying as well as tracking the exploits and the possible actions that cybercriminals take.
- Despite its focus on illicit content, Nulled has a large and active user base.
- Think of Tor as a regular browser like Firefox, Google, or Safari.
- For instance, dark web websites could be infected with malware, or designed as scams to gather stolen data.
- Moreover, due to its popularity, many copycats of the Hidden Wiki exist.
Of course, I absolutely don’t support underage (stuff) and illegal drugs, passport and stuff. I live in a 3rd world country, take a turn down the wrong alleyway and you get to see these things live and real. Considering the internet is literary made and used by humans, these things don’t come as a surprise. As of May 2025, DarkForums has over 12,700 registered users and continues to grow as former BreachForums members seek out a new home. It appears poised to become a long-term fixture in the dark web landscape. So we’ve compiled this huge list of over 15 Subreddits which will help you one way or another in either reaching or understanding the Deep/Dark web.
What Are Some Popular Platforms On Reddit For The Dark Web?
While its .onion address doesn’t make it much easier to maintain an anonymous account, it does make Facebook more accessible in places where it’s censored. The internet’s favorite alternative to Google made a name for itself by not logging your search activity yet still providing decent results. This focus on privacy makes it the Tor Browser’s default search engine and one of the best onion search engines.
While accessing the dark web using Mozilla Firefox is possible, you must first adjust its settings. To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web. In due course, the framework was remodeled and made public as a secure browser. While it might appear tempting to venture into the dark web, it’s crucial to understand that the risks here are far more severe compared to the deep web. Therefore, if you do decide to explore it, exercise extreme caution.
Think about what matters most for your browsing and security, and make informed choices to navigate the dark web safely. Given the explosive growth of these markets, organizations must prioritize proactive threat monitoring. Axis Intelligence provides dark web surveillance solutions that help businesses identify leaked credentials, fraud attempts, and malware risks before they escalate. Some of the reasons why it’s worth monitoring these hack forums include, ability to detect breaches early, gaining threat actor insights, and third-party risk mitigation. If you’re a company, you might want to monitor the dark web to safeguard your reputation and compliance. If you can find your data even before attackers exploit it can help you prevent PR disasters.
Search Code, Repositories, Users, Issues, Pull Requests
People like spies or whistleblowers often contact the CIA via the dark web to keep themselves hidden. To provide freedom of speech and keep journalism a strong pillar of the economy, the BBC made this Tor mirror. It helps people anonymously use the BBC website without restrictions.
To protect your data from the websites you visit, one of the most effective steps is to hide your IP address, which can reveal your location, identity, and browsing habits. Using a virtual private network (VPN) masks your real IP by routing your internet traffic through a secure server, making it appear as though you’re browsing from a different location. A VPN also encrypts your connection, keeping your data safe from surveillance and unauthorized access. It’s simply a part of the internet that isn’t indexed by regular search engines and needs special software, like Tor, to access. However, while browsing the dark web itself is lawful, taking part in illegal activities — like buying or selling illegal goods or engaging in criminal behavior — is not. To stay on the right side of the law, be cautious about what you access and ensure you follow the rules in your region.



