Taking steps to prevent identity theft should be a priority for every single person online. As soon as law enforcement shuts down a major market, a new one will pop up to take its place. The average person has dozens of accounts which form their online identity, all of which can be hacked and sold. This platform has rapidly become a key player in the fraud market, trading in PII and SSH credentials while making use of both the clear and dark web. The market is known for its extensive product listings and reputation system that helps buyers evaluate the reliability of vendors.
AzureStrike – Offensive Toolkit For Attacking Azure Active Directory Environments
The marketplace is well-known for its bug bounty programs and robust security mechanisms, including mandatory 2FA. The darknet marketplace is home to a plethora of illegal and legal activities. However, the markets are dominated by things like illegal drugs, explicit content, pirated files, hacking services, and stolen personal information, among others. Every potential participant’s credentials must be vigorously vetted before they can join. That way, they aim to create secure forums and limit outsiders like law enforcement.
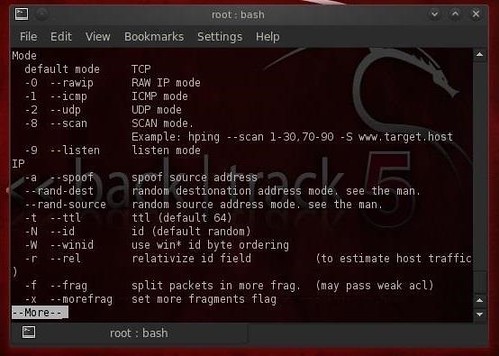
VPN Alternatives For Securing Remote Network Access
Despite a 2019 breach that exposed over 26 million credit cards, it continues to operate, indicating sustained trust in its data pipelines. The series of leaks of U.S. intelligence agency cybertools in recent years1 has put some extremely powerful hacking tools in the public domain and arguably led to an increase in cybercrime. Massive bundles of this professional-grade software are being traded for the price of a beer ($5.64), despite notionally being worth thousands of dollars. This new edition of the Darknet Market Price Index investigates the illicit sale of hacking tools on the dark web. We found that it’s possible to dip your toe into online fraud for less than the price of a coffee.
Our Products
The resulting Index includes prices for WiFi hacking software, phishing pages for big brands, password crackers and much more. Immediately change your passwords, enable two-factor authentication, and notify your bank or credit card provider if the leaked information includes your financial data. You can use dark web monitoring tools, such as NordVPN’s Dark Web Monitor, to check if your data has been leaked. These tools scan dark web forums and marketplaces for any signs of your compromised credentials. There is no need to visit darknet marketplaces yourself to know whether your data was leaked.

How Complex Are Dark Web Marketplaces Currently?
ZeroBin is an encrypted paste tool on the dark web, often used for sharing messages or files without storing user data. Yes, Onion.live and Haystak provide real-time updates and search functionalities for .onion sites. Use a VPN, access the dark web only through the Tor browser, avoid logging in with personal credentials, and use virtual machines for isolation.
What Is Onionlive Used For?
Therefore, you need to take your privacy seriously and start by using strong and unique passwords for every online account you open. The sad reality is the fact that law enforcement agencies can’t track and prosecute perpetrators or even take down such content given the anonymous nature of the dark web. As much as authorities work hard to shut down various sites, it shows what the dark web is capable of doing if left unchecked. The internet is a wide landscape that comprises the surface part – the internet that we all know and the hidden portion.

The Dangers Of Darknet Marketplaces

While it might be tempting, remember that downloading such content has serious legal and cybersecurity risks. Want to get illegal drugs, fake passports, Trojan, or other cyber attack software? Next up is Abacus, another newer market that has already made a massive name for itself, especially following AlphaBay’s closure.
By pooling knowledge and technical capabilities, stakeholders can mount a more unified defense, slowing the growth of cybercrime and reducing its impact on businesses and individuals worldwide. Despite its name, Russian Market serves a global audience and primarily uses English for communication. It is known for its relatively affordable prices and diverse product offerings, which include RDP access credentials, stealer logs, and other cybercrime tools. The platform also boasts specialized utilities like a PayPal cookie converter, catering to fraudsters looking to exploit payment gateways.
- Prices were collected in USD and converted to GBP using the exchange rate at the time of listing ($1.31 rate).
- We also found anonymous SMS and phonecall spoofers for use in scams, each costing less than $1.
- Implementing preventive security measures can significantly lower the chances of data breaches, unauthorized access, and financial fraud.
- In this post, we’ll walk you through the top 10 dark web marketplaces that you need to watch for potential threats to your organization.
Use strong, unique passwords for each of your accounts, enable two-factor authentication whenever possible, and be cautious about clicking on links or downloading attachments from unknown sources. A Remote Access Trojan works by deceiving a user into downloading and installing the software on their system. The software is usually disguised as a legitimate program or file, and once installed, it gives the attacker complete control over the victim’s computer. The attacker can then use the RAT to perform a variety of malicious activities, including stealing sensitive data, installing additional malware, and modifying system settings. Exploit kits are a more sophisticated type of tool that hackers use to exploit vulnerabilities in software programs and operating systems.
Tor remains the most prevalent method due to its ease of use and robust anonymity features, but the popularity of I2P is steadily growing due to its increased resistance to surveillance and censorship. Remote desktop protocol (RDP) clients and server software are also in demand. DDoS services and tools are offered for sale on dark web hacking forums, marketplaces and chat applications. Many phishing tools can be found on Hacking forums, and chat applications such as Telegram and dark web marketplaces. Another notable departure from the scene was the ASAP market, which has been active since at least 2020. It had catered to illicit drugs and psychedelics vendors, as well as offering stealer logs and payment card information.
Many “trusted” sellers use fake reviews or steal reputations from shutdown markets. The evolution from IRC to Telegram represents more than just a shift in tools, it signals a transformation in how cybercrime infiltrates daily digital life. Criminals no longer retreat to hidden enclaves; they co-opt mainstream platforms.
Below you’ll find a table showing some of the major darknet markets Krixo has detected, their URLs, and their current status. Background research tasks included learning from past drug lords, researching legal matters, studying law enforcement agency tactics and obtaining legal representation. Patterns recommended to avoid include hiring hitmen like Dread Pirate Roberts, and sharing handles for software questions on sites like Stack Exchange. Dark web markets work much like regular e-commerce websites but with extra layers of anonymity and encryption.



