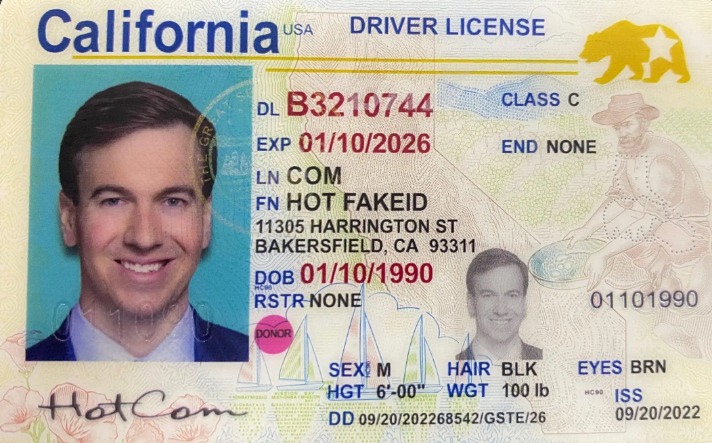
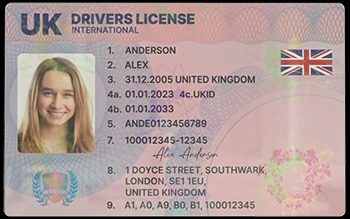
To mitigate the risk of ever-improving AI fraud, businesses must have AI-ready methods of their own, by way of best-in-class identity solutions. Our study revealed that the quality of fake IDs, analyzed through various physical and software-based fraud prevention tools, varied state by state. While states such as New York, Texas, and Arizona see the most frequent use of fake IDs, according to IDScan.net’s 2023 and 2024 Annual Fake ID Reports, they were also the easiest to catch.
We work with businesses of all sizes to provide scalable solutions to their identity verification challenges. However, fraud tools like Cloud Passport have likely not examined enough IDs and passports to create truly 1-to-1 fake IDs using AI. And there are multiple layers of protection that businesses can easily implement to make fraud more difficult, even with the use of an AI-generated fake ID. In the thread were dozens of messages, many in Russian, discussing availability of various fake document formats (both drivers licenses and passports). Linked from the Telegram thread is the .RU site Passport Cloud, which has a fake ID generator with a user friendly interface and a familiar face on the sample ID. Passport Cloud claims to have examined 5,000 drivers licenses to build their AI.
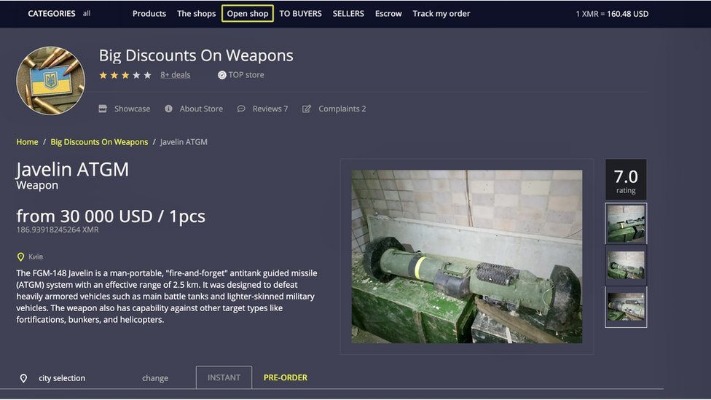
Platforms And Marketplaces On The Dark Web

Fake IDs are a growing concern for businesses, law enforcement, and individuals alike. With the rise of advanced technology, creating high-quality fake IDs has become increasingly easier. These counterfeit IDs can be used for various purposes, including identity theft, underage drinking, and financial fraud.
Rise Of AI-Generated Fake IDs
These ultra-realistic fakes replicate every detail, down to wear-and-tear marks and scanned barcodes, making them indistinguishable to human employees and often fooling outdated scanners. Even trained teams equipped with state-of-the-art tools can find themselves outmatched. Your journey toward faster, more accurate identity verification starts here. In one case, a scammer used deepfake software and a ring light to impersonate an elderly man during a video call, convincing a woman to send money. Behind the real-time avatar was a much younger individual with a completely different appearance.
Final Thoughts On Best Replica ID Features
- Her work delves deep into the rich cultural heritage of the Gullah community, exploring their traditions, challenges, and contributions to American society.
- Unlike traditional identity theft, synthetic identities contain just enough accurate information to make them plausible, surpassing past basic level identity checking resources.
- As a global IDV provider, Veriff understands local nuances and has experience handling various fraud types across different regions.
- These identities are used by criminals for fraud, such as opening fake accounts, obtaining credit, or committing financial crimes without detection.
- Image of counterfeit ID card and underground economy tools Artificially generated image.
It is a reliable messaging tool where you copy/paste a text or image and send it to your addressee. Cryptocurrencies such as Bitcoin have been the dark web currency even before they became available to the general public. Right now, you can use many cryptocurrency .onion sites to buy or sell all types of cryptocurrencies. Using the ProtonMail .onion site offers security and privacy advantages.
Agentic AI Workflows: Strategies For Risk Management And Fraud Investigations
Dark web marketplaces, encrypted messaging apps, and 3D printing have enabled fraudsters to produce realistic-looking IDs at a low cost. These stats reveal how common the issue is becoming, even among teenagers as young as 15. It’s estimated that 95% of all standard customer onboarding processes fail to detect the presence of fake identification. This can lead to a direct average loss of US $15,000 per incident for organizations, and in some situations, this is far more. A criminal may develop a new identity using sophisticated AI-enabled technology that makes it highly credible.
Internet of Things (IoT) devices and critical infrastructure have become prime targets for AI-powered cyberattacks due to their often-inadequate security protocols and pervasive connectivity. Cybercriminals leverage AI algorithms to efficiently scan, identify vulnerabilities, and coordinate large-scale attacks on connected devices and infrastructure systems, significantly increasing potential damage and disruption. Offers complex ID features, including raised text and scannable barcodes. Talk to our cybersecurity experts at WebOrion and let us help you stay two steps ahead of the bad guys. These are used for fraud, SIM swaps, opening bank accounts, or even crypto KYC bypassing.
From underage students trying to enter bars to identity thieves targeting financial systems, the misuse of identification has evolved significantly. This article dives deep into the data, examining how fake ID usage is tracked, who’s most likely to use one, and what steps are being taken to prevent it. Simple KYC methods do not spot these fake identities, creating a prolonged risk of loss.

Despite its name, the marketplace operates primarily in English and serves a global audience. It has gained a reputation for being a reliable source of high-quality data for cybercriminals. Beginning in September 2021, Abacus Market has established itself as one of the leading dark web marketplaces. After AlphaBay closed, Abacus Market took its place as the world’s largest underground darknet marketplaces. Abacus Market quickly rose to prominence by attracting former AlphaBay users and providing a comprehensive platform for a wide range of illicit activities.
UK MPs Get AI Fake IDs, Chaos Ransomware Loses Millions, And Dark Web Forums Eat Themselves
In the U.S., several states have passed new legislation targeting online fake ID sellers and increasing surveillance of digital marketplaces. They come with encoded magnetic strips, RFID chips, and barcodes that mimic legitimate data. These features allow fakes to pass basic verification scans at clubs, bars, and retail establishments. As more venues rely on digital scanning rather than visual checks, fake ID creators have stepped up their game to include embedded data that appears authentic. The advent of quantum computing, expected to mature significantly within the next five years, could fundamentally disrupt current cybersecurity models.

Can WiFi Owners See Your Internet History?
Although counterfeit documents might initially seem attractive due to perceived convenience or anonymity, the dangers far outweigh any temporary benefits. Users face significant legal penalties, including hefty fines, criminal charges, imprisonment, and permanent damage to their personal and professional reputations. Fake IDs and passports are predominantly sold through hidden online marketplaces accessible via the dark web. Additionally, use of AI-generated fake ID images often comes with specific digital behaviors which can be monitored and flagged in the digital identity verification process. These suspicious activities can trigger a deeper review of the ID image and face match, which allows verification tech to better stop fraudsters.

Armed with knowledge, critical thinking, and robust security practices, you can uncover meaningful, valuable content that challenges the dark web’s often one-sided reputation. By implementing these verification strategies—using curated lists, cross-referencing multiple sources, and employing cryptographic keys—you can dramatically reduce the likelihood of visiting fake or dangerous dark web sites. While no approach guarantees complete safety, a careful and skeptical mindset serves as one of your most valuable tools on the hidden internet. Finding reliable sites on the dark web can feel like a guessing game—many onion addresses appear cryptic, and their ever-changing nature makes it challenging to build trust. However, the quality of the resources you choose to engage with can make all the difference in ensuring a safer, more productive experience.
Editing Real IDs
Optical Character Recognition (OCR) and barcode scanning are common tools used to speed up ID checks. However, these systems were built to extract readable data—not verify the authenticity of the document itself. If a fake ID contains clean, scannable text or a functioning barcode, it may pass through undetected. For example, some legitimate Florida driver’s licenses have barcodes that are difficult for standard scanners to read due to printing issues. This highlights how fragile these systems can be, especially when asked to flag more complex or deliberate fakes.
How To Use Fake IDs Safely (If At All)
Real ID cards can be identified by a star, usually black or gold, in the upper corner of the ID. In late March, OpenAI added new image generation capabilities to its star product ChatGPT. The update went viral, resulting in a deluge of Studio Ghibli-inspired AI-generated images posted across social media and drawing millions of users to the platform. Throughout this guide, we’ve explored the legal and ethical considerations of venturing into the dark web, how to enhance security and anonymity, and the criteria for identifying trustworthy resources. There are a few common factors we saw when generating deepfake ID images. Note that we are being intentionally vague in this section because we do not want to help fraudsters create better fake ID images.